Vmware sso что это
vCenter Server 7 has an internal user database that allows you to add and manage users very easily. User management and Single Sign-On are provided by the embedded Platform Service Controller (PSC). The PSC runs other services, such as licensing, certificate services, authentication framework, or appliance management.
Vladan Seget is an independent consultant, professional blogger, vExpert 2009-2021, VCAP-DCA/DCD and MCSA. He has been working for over 20 years as a system engineer.
- How to use VMware vSAN ReadyNode Configurator - Fri, Dec 17 2021
- VMware Tanzu Kubernetes Toolkit version 1.3 new features - Fri, Dec 10 2021
- Disaster recovery strategies for vCenter Server appliance VM - Fri, Nov 26 2021
You can also configure vCenter Server 7 to authenticate the connection via your Microsoft Active Directory (AD), so any users that you'll grant access to part of your vSphere infrastructure will not need to remember new login/password combination, but will use the Windows session credentials.
Single Sign-On allows different vSphere components to communicate with each other via a secure token mechanism (SAML).
The SSO domain that you create when you first install vCenter Server is the default identity source of the vSphere environment. You can set the Microsoft AD integration afterwards. VMware SSO allows not only Active Directory authentication, but also any other Security Assertion Markup Language (SAML) 2.0–based authentication source.
New in vSphere 7.0, vCenter Server supports federated authentication to sign in to vCenter Server.
vCenter Single Sign-On Administrator Users
The vCenter Single Sign-On administrative interface is accessible from either the vSphere Client or the vSphere Web Client .
To configure vCenter Single Sign-On and manage vCenter Single Sign-On users and groups, the user administrator@vsphere.local or a user in the vCenter Single Sign-On Administrators group must log in to the vSphere Client . Upon authentication, that user can access the vCenter Single Sign-On administration interface from the vSphere Client and manage identity sources and default domains, specify password policies, and perform other administrative tasks.
Note: You cannot rename the vCenter Single Sign-On administrator user, which is administrator@vsphere.local by default or administrator@ mydomain if you specified a different domain during installation. For improved security, consider creating additional named users in the vCenter Single Sign-On domain and assigning them administrative privileges. You can then stop using the administrator account.
Настройка Active Directory as a LDAP Server
И еще хочу показать, как настроить SSO через Active Directory as a LDAP Server, то же распространенный метод. Давайте просто пробежимся, по нужным полям.
Минусом данного решения, является, то что если контроллер домена не доступен, то вы не сможете пройти аутентификацию
- Name > указываете любое понятное вам имя, оно не на что не влияет
- Base DN for users > поиск по пользователям
- Dmain name > FQDN имя домена
- Domain alies > краткое имя домена
- Base DN for groups> поиск по группам
- Primary server URL > LDAP сервер
- Secondary server URL > LDAP сервер
- Username > имя пользователя, от имени которого будет подключение к AD
- Password > пароль
После ввода данных, нажмите кнопку Test Connection, для понимания того, получилось ли подключиться по LDAP.

В принципе этих двух методов, достаточно для настройки SSO в VMware VirtualCenter Server,
When a user logs in to a vSphere component or when a vCenter Server solution user accesses another vCenter Server service, vCenter Single Sign-On performs authentication. Users must be authenticated with vCenter Single Sign-On and have the necessary privileges for interacting with vSphere objects.
- Solution users represent a set of services in your vSphere environment. During installation, VMCA assigns a certificate to each solution user by default. The solution user uses that certificate to authenticate to vCenter Single Sign-On . vCenter Single Sign-On gives the solution user a SAML token, and the solution user can then interact with other services in the environment.
- When other users log in to the environment, for example, from the vSphere Client , vCenter Single Sign-On prompts for a user name and password. If vCenter Single Sign-On finds a user with those credentials in the corresponding identity source, it assigns the user a SAML token. The user can now access other services in the environment without being prompted to authenticate again.
Which objects the user can view, and what a user can do, is usually determined by vCenter Server permission settings. vCenter Server administrators assign those permissions from the Permissions interface in the vSphere Web Client or the vSphere Client , not through vCenter Single Sign-On . See the vSphere Security documentation.
Single Sign-on uses several services ^
- Authentication of userss—Users are authenticated through either an external identity provider federation or the vCenter Server built-in identity provider. The built-in identity provider supports local accounts, Active Directory or OpenLDAP, integrated Windows authentication (IWA), and other authentication systems such as smart card, RSA SecurID, and Windows session authentication.
- Authentication of solution users through certificates.
- Security Token Service (STS)—This service issues the SAM tokens representing a user's identity.
- SSL for secure traffic.
Настройка Single Sign-On
Установку Single Sign-On мы производили в момент установки VMware VirtualCenter Server, посмотреть можно вот тут, там и задавался пароль для административной, учетной записи administrator@vsphere.local. Я же хочу показать, как настроить SSO, чтобы вы могли раздавать права пользователям Active Directory в VMware VirtualCenter Server.

В итоге у вас появится возможность перейти на сайт.

У вас откроется форма ввода логина и пароля.

Далее переходим в административный раздел, вкладка Administration.

Далее идем в Configuration > identity Sources и нажимаем кнопку плюсик, для добавления подключения к Active Directory.

в окне identity Source у вас будет вот такой выбор:
- Active Directory (integrated Windows Autentification)
- Active Directory as a LDAP Server
- Open LDAP
- Local OS

Users and groups ^
Users and groups is also found in the same section. We can have a look at the Local Accounts tab. On the Local Accounts tab, you'll see different options where you can change the password policy or password expiration lifetime.
By default, users are locked out after five consecutive failed attempts in three minutes, and a locked account is unlocked automatically after five minutes. You can change these defaults using the vCenter Single Sign-On lockout policy.
You should know that many of these groups are internal to vsphere.local domain or give users high-level administrative privileges. You should only consider adding users to those groups after cautious consideration of the risks.
You should never delete any predefined user or group.

Possibility to change local password policy
Final thoughts ^
vCenter Server 7 has very complete management of identity sources and providers. We have also looked at some basics of SSO groups and users. However, I'd strongly recommend reading other lessons from our free study guide and also getting the complete VMware documentation set for vSphere 7.
The study guide will help you to pass VMware Certification VCP-DCV 2020 based on vSphere 7. The whole study guide, available here, helps you master all the topics to become VMware Certified.

SSO Configuration: Identity providers and sources ^
Open your vSphere web client and connect to your vCenter Server 7, then go to Shortcuts > Administration.

Access VMware SSO via Administration
Click the Single Sign-On section and Configuration. On the Identity provider tab, click Active Directory Domain > Join AD.

Join Microsoft AD
Enter your Microsoft domain and OU (optional). After entering your Microsoft AD credential, you'll need to reboot.
I thought that VMware is better than Microsoft, but both vendors' products need a reboot when changing Microsoft AD specifications, changing domain, going from workgroup to domain, etc.

Join Microsoft AD and reboot the appliance
If you do not join the VCSA to Microsoft AD, you'll get the following message when you want to change the identity source:
You can't continue because the vCenter Single Sign-On server is not currently joined to any domain.

Change identity source type
After a reboot, go back to the identity sources. You should now be able to pick the Microsoft AD.
I found it quite convenient when working on a Windows workstation attached to a Microsoft domain to simply tick the check box "use Windows session authentication" when connecting to vCenter Server.
If the checkbox is grayed out, you'll need to install the Enhanced Authentication Plug-in.

Use Windows session authentication is grayed out
The Enhanced Authentication Plug-in enables:
- Accessing the VM console
- Deploying OVF or OVA templates
- Transferring files with the datastore browser
- Using Windows session authentication
Note: If you configure vCenter Server to use federated authentication with Active Directory Federation Services, the Enhanced Authentication Plug-in only applies to configurations where vCenter Server is the identity provider (Active Directory over LDAP, integrated Windows authentication, and OpenLDAP configurations).
Back to our SSO identity provider configuration, where you can see how I'm adding the Microsoft AD as the identity source type.

Add Microsoft AD as the identity source type
How to Log In to vCenter Server Components
You can log in by connecting to the vSphere Client or the vSphere Web Client .
When a user logs in to a vCenter Server system from the vSphere Client , the login behavior depends on whether the user is in the domain that is set as the default identity source.
If your environment includes an Active Directory hierarchy, see VMware Knowledge Base article 2064250 for details on supported and unsupported setups.
Note: Starting with vSphere 6.0 Update 2, two-factor authentication is supported. See Understanding vCenter Server Two-Factor Authentication.
I was until I dived in and found answers which I will do my best to explain here.
vCenter Single Sign-On is a new feature of vSphere 5.1 that is not just an authentication broker but also a security token exchange providing a more secure way of accessing your vSphere solutions. What that means is that when you previously logged into vCenter Server, you were authenticated with the provided username and password against the Active Directory configured for vCenter Server. With vSphere 5.1 and vCenter Single SIgn-On you no longer log directly into vCenter Server but with a security domain defined by your vSphere environment. When logging in to vSphere 5.1 you actually pass authentication to the vCenter Single Sign-On server which can be configured with multiple identity sources like Active Directory and OpenLDAP and on successful authentication, your username and password is exchanged for a security token which is then used to access the vSphere components like vCenter Server and vCenter Orchestrator etc.

Although vCenter SIngle Sign-On is an additional component in the vSphere suite, a critical component that is required before any other vSphere 5.1 component is installed or upgraded, it actually doesn’t necessarily mean you need to re-architect your vSphere environment. You can use vSphere just as you have been from years past and vCenter Single Sign-On will fit right on in just as an additional service local too or separate from vCenter Server.

Where some of the confusion comes from I believe is with the added benefits that vCenter Single Sign-On can bring when administering multiple vSphere environments. When installing vCenter Server you have the choice to specify or install a vCenter Single Sign-On server providing the ability to add multiple vCenter Servers and their components to a centralized vCenter Single Sign-On source. This provides a single pane of glass view across all vCenter servers, 5.0 and higher for administration as well as the ability to define queries that can be searched across multiple vCenter Servers without the requirement of Linked Mode used in the past.
Now this maybe seen as a single point of failure, a critical one at that when talking authentication but vCenter Single SIgn-On can be configured in a clustered or multisite deployment to help with availability.
Clustered deployments are with multiple instances of vCenter SIngle Sign-On are deployed, one is defined as a primary instance the remainder as slaves and all share a single database instance and placed behind a third party load balancer can provide redundancy or high availability of the vCenter Single Sing-On solution. This typically is local to a single site however if geographical sites are used with multiple vCenter servers, you can still utilize a central clustered environment, however a multisite configuration is recommended.

Multisite deployments are where a local replica is maintained at remote sites of the primary vCenter Single SIgn-On instance. vCenter Servers are reconfigured to use the local vCenter SIngle SIgn-On service and reduce authentication requests across the WAN. Multisite deployments do drop the support of single pane of glass views unless Linked Mode is utilized and multisite deployments are actually required to maintain Linked Mode configurations where roles, permissions and licenses are replicated between linked vCenter servers. Linked mode will re-enable single pane of glass views across multisite instances.
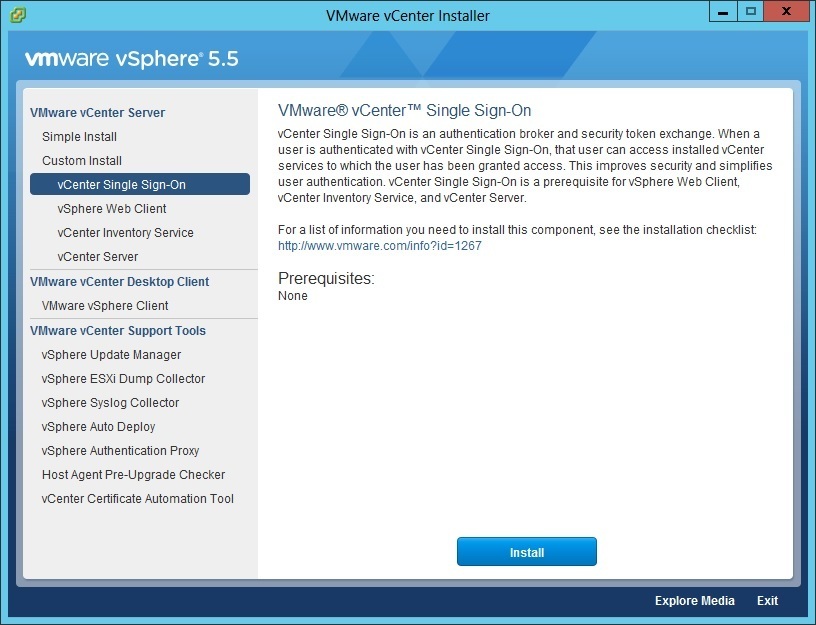
You can install vCenter SSO using the VMware vCenter Installer. Two installation options are supported:
1. use the Simple Install option to deploy the basic mode. This option installs vCenter SSO, vCenter Server, vSphere Web Client and vCenter Inventory Service on the same host and it is appropriate for most deployments. The Simple Install method is explained here .
2. use the Custom Install option to install the multisite or HA mode. This option enables you to install vCenter SSO separately from vCenter Server, vCenter Inventory Service or vSphere Web Client. This is often recommended for medium to large environments.
You can also use vCenter Server Appliance , which is a preconfigured SUSE Linux-based virtual machine optimized for running vCenter Server and the associated services, such as vCenter SSO.
In this section we will describe how to install vCenter SSO using the Custom Install option.
To start the installation, select vCenter Single Sign-On from the VMware vCenter Installer:
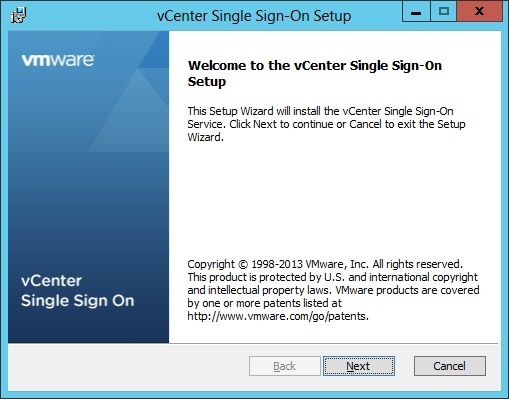
Click Next to start the setup:
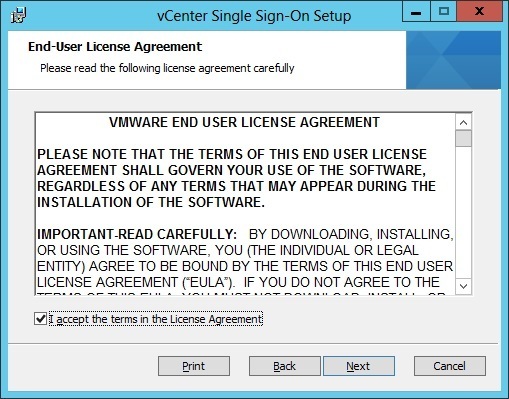
Accept the license agreement and click Next:
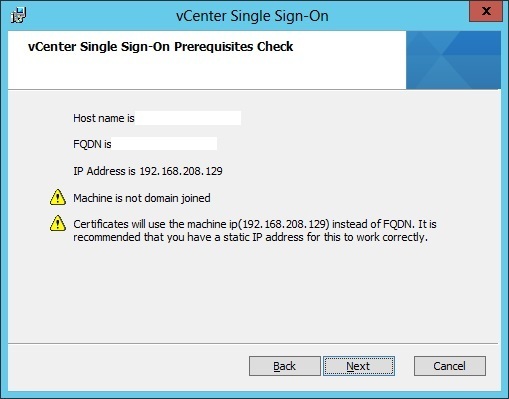
Verify the prerequisites and click Next:
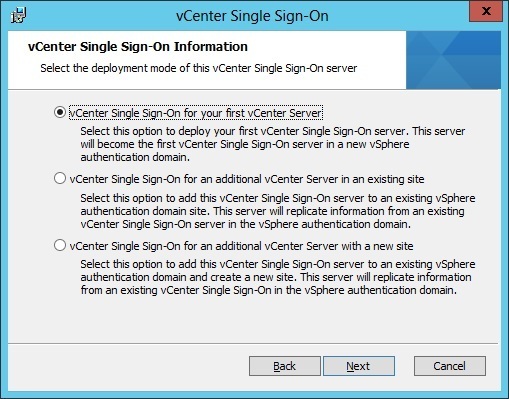
Select the deployment mode. Three modes are available. In this is your first vCenter SSO installation, select the first option and click Next:
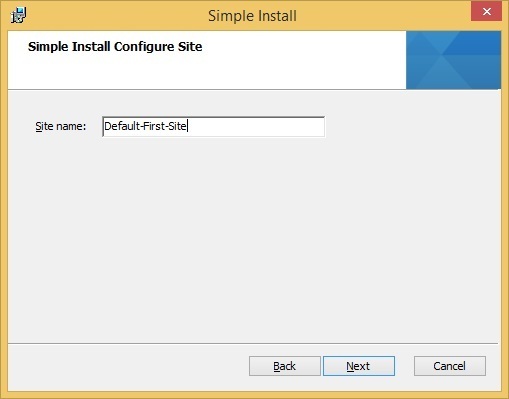
Choose a site name. The site name is used in environments where there are SSO servers in multiple sites.
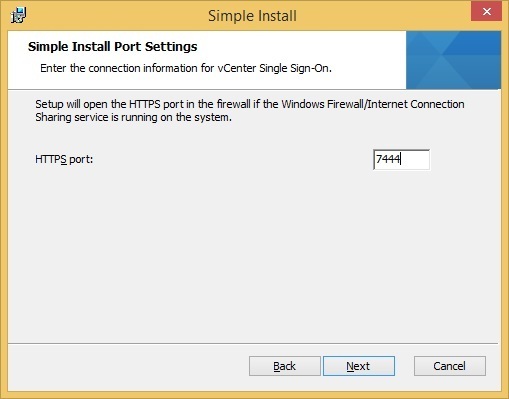
Next, you are prompted to choose the TCP port number for the SSO service. You can leave the default value of 7444 in most cases:
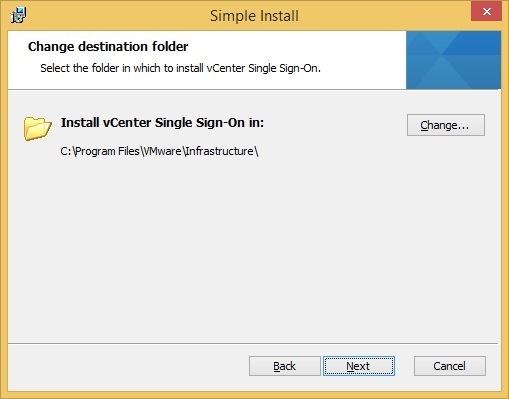
Choose the install location and click Next:
Review the install options and click Install to start the installation:
vCenter Single Sign-On and vCenter Server Users
Users authenticate to vCenter Single Sign-On by entering their credentials on the login page. After connecting to vCenter Server , authenticated users can view all vCenter Server instances or other vSphere objects for which their role gives them privileges. No further authentication is required.
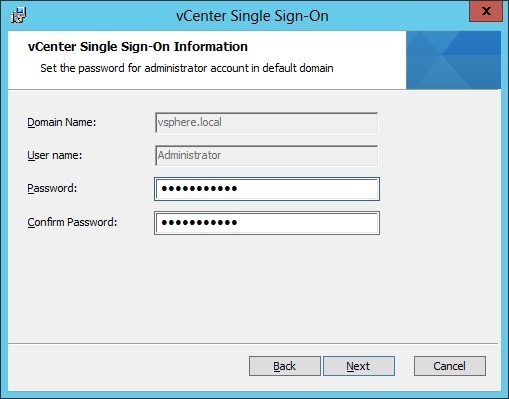
After installation, the administrator of the vCenter Single Sign-On domain, administrator@vsphere.local by default, has administrator access to both vCenter Single Sign-On and vCenter Server . That user can then add identity sources, set the default identity source, and manage users and groups in the vCenter Single Sign-On domain.
All users that can authenticate to vCenter Single Sign-On can reset their password, even if the password has expired, as long as they know the password. See Change Your vCenter Single Sign-On Password. Only vCenter Single Sign-On administrators can reset the password for users who no longer have their password.
Note: When you change the password for your SDDC from the vSphere Client , the new password is not synchronized with the password that is displayed on the Default vCenter Credentials page. That page shows only the Default credentials. If you change the credentials, you are responsible for keeping track of the new password. Contact Technical Support and request a password change.
Что такое SSO
Давайте для начала разберемся, что такое Single Sign-On (SSO) и как эта технология работает. Если в двух словах, то это механизм единого входа в систему или в приложения, где одна есть куча корпоративных сервисов, которые благодаря базе данных SSO, идентифицируют вас и автоматически предоставляют доступ к корпоративным ресурсам, без вашего участия (повторного ввода логина и пароля)

Сама VMware настоятельно рекомендует производить установку SSO вместе с сервером vCenter. Одна версия SSO может обслуживать до 1000 хостов ESXi и 10 000 виртуальных машин.
- Поддержка односторонних и двусторонних AD-трастов
- Поддержка нескольких лесов
- Можно использовать локальную аутентификацию без домена, если это необходимо
- Появилось множество средств для траблшутинга и диагностики решения
Зеленым отмечено, какие компоненты можно настраивать с помощью Single Sign-On

ESXi Users
Standalone ESXi hosts are not integrated with vCenter Single Sign-On or with the Platform Services Controller . See vSphere Security for information on adding an ESXi host to Active Directory.
If you create local ESXi users for a managed ESXi host with the VMware Host Client , vCLI, or PowerCLI, vCenter Server is not aware those users. Creating local users can therefore result in confusion, especially if you use the same user names. Users who can authenticate to vCenter Single Sign-On can view and manage ESXi hosts if they have the corresponding permissions on the ESXi host object.
Настройка Active Directory (integrated Windows Autentification)
Настройка Active Directory (integrated Windows Autentification), как метода аутентификации, наверное самая простая, от вас потребуется две вещи:
- Чтобы сервер VMware VirtualCenter Server был присоединен к домену
- Вы должны в настройках указать название доменного имени

Преимущество, что данный метод, настраивается за пол минуты, но он менее безопасный, по сравнению использованием SPN имени. Первым делом вам нужно проверить нет ли у вас для вашего VMware VirtualCenter Server созданного SPN. Формат команды в командной строке Windows вот такой:

Думаю вы в первый раз уж точно получите, что SPN не найден. Далее нам его нужно задать для SSO.
Далее заполняете нужные поля в Active Directory (integrated Windows Autentification)

Кстати можно посмотреть в Active Directory параметр в учетной записи службы, где прописывается ServicePrincipalName

vCenter Server object hierarchy ^
All objects in the vCenter Server hierarchy can carry permissions that are assigned by you. You can pair a user and a role with the object. For example, you can select a resource pool and give a group of users read privileges to that resource pool object by assigning them a specific role.
However, for some services that are not managed by vCenter Server directly, you'll need to be a member of certain SSO groups that determine the privilege. For example, a user who is a member of the Administrators group can manage vCenter Single Sign-On. A user who is a member of the CAAdmins group can manage the VMware Certificate Authority, etc.

Example of CAAdmins group
Читайте также:


