Mikrotik грузит процессор dns
Бывают ситуации, когда нужно сохранить часть настроек, например, правила фаервола, скрипты, NAT, правила маркировки пакетов и т.п. Для этого помогут следующие команды:
ip address export file=ip.rsc
ip firewall mangle export file=mangle.rsc
ip firewall nat export file=nat.rsc
ip firewall filter export file=filter.rsc
queue simple export file=simple.rsc
ip dns export file=dns.rsc
files backup export file=backup.rsc
system script export file=script.rsc
system scheduler export file=scheduler.rsc
tool e-mail export file=email.rsc
ip firewall address-list export file=address-list.rsc
ip route export file=route.rsc
ip dhcp-server network export file=network.rsc
queue type export file=type.rsc
queue tree export file=tree.rsc
queue simple export file=simple.rsc
interface ethernet export file=ethernet.rsc
ip pool export file=pool.rsc
ppp profile export file=profile.rsc
log export file=log.rsc

1. Первым делом заходим в Tools->Profile, выбираем Cpu - all и нажимаем кнопаньку Start
2. Смотрим и видим, что высокая загрузка у службы DNS

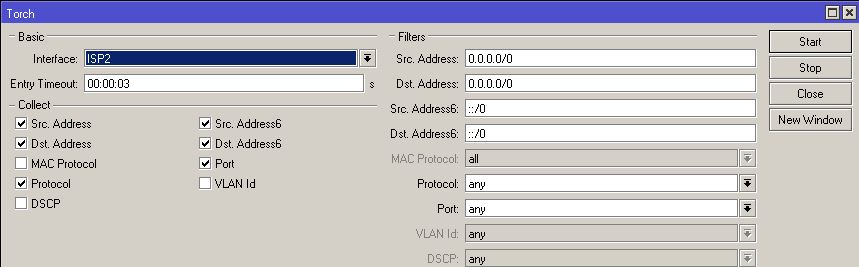
3. Затем открываем Tools->Torch, выбираем входящий интерфейс, в моем случае это Beeline, галки ставим как на скрине и запускаем Start.
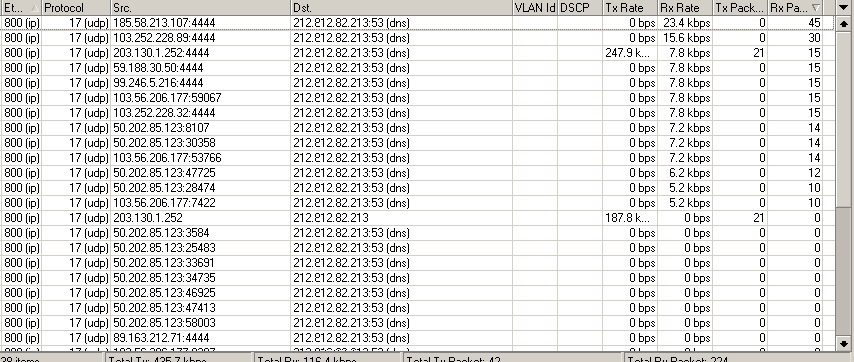
Теперь мы видим кучу запросов с разных IP адресов к нам на 53-й порт. Вот они и грузят наш процессор.
- Все IP – адреса, пакеты с которых приходят на 53 порт нашего Микротика будут помещаться в специальный лист с названием dns spoofing на 1 час.
- Каждый IP – адрес, с которого будет поступать запрос на 53 порт будет проверяться на предмет нахождения в списке dns spoofing . Если он там есть, мы будем считать, что это DNS – спуфинг с частотой реже чем раз в час и будем дропать данный пакет.
Chain = input - обрабатываем приходящие пакеты
Protocol = UDP - нас интересуют пакеты, у которых в качестве транспорта используется UDP
Dst. Port = 53 - портом назначения должен быть 53 порт, то есть DNS служба
In. Interface = Beeline - проверка подвергаются все пакеты, которые приходят на интерфейс Beeline, который смотрит в публичную сеть.
Action = add src to address list - в качестве действия, мы будем добавлять IP – адрес источника в специальный лист
Address List = dns spoofing - указываем имя листа, в который добавляем IP
Timeout = 01:00:00 - добавляем на 1 час
Теперь добавим 2-е правило:
Src. Address List= dns spoofing - указываем Микротику, производить проверку приходящего пакета на предмет нахождения в указанном листе
Action = drop - если IP – адрес пакета есть в указанном списке, то дропаем этот пакет.
Всем привет! Имею более 5 установленных SOHO роутеров микротик, в разных местах от разных провов, и с разной пропускной скоростью. И начал замечать, что время от времени загрузка роутеров приближается где-то к 100%, на других вываливается связь из-за малой пропускной способности инет-канала. Как выяснилось, причиной всего это во всех случаях какая-то нездоровая активность на DNS сервер Микротика которая либо забивает канал, либо если канал широкий съедает все cpu. Причем на всех установленных роутерах - внешние айпи адреса.
Настраивал все по мануалам, в фаерволле никаких правил не добавлял. Убрал только доступ к микротику, оставив WinBox.
Подскажите, как правильнее закрыть 53 порт? Что бы внутри ничего не нарушить :)
Оценить 1 комментарий
заблокировано файрволом все что можно - не помогает
в winbox'e
IP - DNS - Static - выделяешь свой роутер и жмешь disable - нагрузка сразу упадет


То же самое было около года назад. Решилось закрытием 53 порта.
chain input; Dst Adress @твой IP
Protocol 6 (tcp)
Dst port 53.
action drop
(или при желании добавлять эти адреса флудеры в список и банить тот список на определенное время)
И еще 1 правило такое же правило для UDP
Protocol 17 (udp)

What's new in 6.22 (2014-Nov-11 14:46):
*) ovpn - added support for null crypto;
*) files - allow to remove empty disk folders;
*) sntp - fix problems with dns name resolving failures that were triggering
system watchdog timeout;
*) eoip/eoipv6/gre/gre6/ipip/ipipv6/6to4 tunnels have new features:
tunnels go down when no route to destination;
tunnels go down for 1 minute when transmit loop detected, warning gets logged;
new keepalive-retries setting;
keepalives enabled by default for new tunnels (10sec interval, 10 retries);
*) improved connection-state matcher in firewall - can match multiple states in one rule, supports negation;
*) added connection-nat-state matcher - can match connections that are srcnatted,dstnatted or both;
*) 100% CPU load caused by DNS service fixed;
*) 100% CPU load caused by unclassified services fixed;
*) 6to4 tunnel fixed;
*) new RouterBOOT firmware for Metal 2SHPn to improve wireless stability;
Подскажите, как это правильнее сделать, потому как в фаерволе я запретил: input, source_adr 0.0.0.0/0 , dst. adr свой_внешний_айпи , 53 tcp. После чего внутрисети начались сложности с "резолвингом" адресов и пр.
ну если их десяток, и запросы не интенсивные, тогда хватит
а так - не слабый RB2011UiAS-RM тянущей у меня полтора гигабита на nat, начитает захлёбываться уже при паре десятков DNS трафика
Mon Jan 14, 2013 4:09 pm
I've been using Mikrotik's DNS Cache server and notice that every hour for anywhere from 30 seconds to a minute and a half, DNS queries fail. I can still ping by IP but not by name. Looking at the profiler, I can see that DNS consumes 100% of CPU during this time, which is followed by Flash consuming much CPU and then unclassified. I do have approximately 10000 static entries. I presume this is part of the issue. I am running a RB1200 with 1.5GB RAM on the latest, RouterOS 5.22. I have played around with allocating various amount of memory to DNS to no avail. Is it true that 10M is max memory that can be used for DNS?
I am not sure where to begin troubleshooting this issue. Any thoughts on where to begin tracking down this problem?
MikroTik Support
Mon Jan 14, 2013 4:46 pm
what you have set up in /ip dns settings? (except static entries) what is cache usage and how much cache you have free?
Mon Jan 14, 2013 5:02 pm
servers: 8.26.56.26,8.20.247.20,198.153.192.40,198.153.194.40,
8.8.4.4,8.8.8.8
dynamic-servers:
allow-remote-requests: yes
max-udp-packet-size: 512
cache-size: 10240KiB
cache-max-ttl: 1w
cache-used: 10062KiB
Previously, I've used up to 4096 as max-udp-packet-size and I've allocated as much as 128MB to cache. It doesn't appear to solve it.
By dumb luck, I may have stumbled upon it. I had my Dude server down during the last hour's interval and DNS did not go down. Perhaps something in the Dude is hammering my DNS? For now, on the Dude I've disabled the monitoring of the DNS service on this router. Any ideas what other settings in the Dude would do this? I've switched so that machine is not using this router as DNS at all now also. At the next scheduled interval, I will see if the behavior has changed and report back.
Does anyone know what the max cache-used can be for DNS proxy? I saw in the documentation 10240KB, but it allows you to put in higher values.
Mon Jan 14, 2013 7:57 pm
Well I disabled a bunch of DNS type of settings in the Dude and it still does it. When I'm in winbox and DNS is consuming 100% of CPU, in IP->DNS, it shows "allow remote requests" as unchecked and no servers are filled in. Would this be due to winbox not having loaded all the way or perhaps it is actually not caching at that point? Perhaps I should be running DNS on a separate server? Do you guys recommend Power DNS or BIND or another? I'd like to use my rather large block list either way.
Thu Jan 31, 2013 6:31 pm
Frego - I am having the same problem with my rb450g. If I turn on "allow remote requests" the CPU almost immediately went to 100%. Now, I was tinkering with it and turned that option from on to off and then on again when the cache had about 400 items in it. (around 200 IPs were using it for caching)
I just now flushed it and turned it back on again. Cache starting to refill, CPU at around 10% right now.
Software is 5.22
MAX UDP packet size is 512
cache size is 10240
I have only my upstream providers DNS IPs in the Mikrotik at this point. (Under DNS settings, and also under Static, and DHCP server DNS settings.
I would like to know what fixes this.
Thu Jan 31, 2013 9:21 pm
OK, I have had this running for a little while now. I currently only have about 40 IPs using the cache/DNS.
Roughly 350 items in the cache, CPU is now 50%-60% load.
I have a maximum of 13MB of data going through it.
Mon Feb 18, 2013 5:15 am
I have an update to report. I have disabled DNS on the router I was having this problem with. However, I still have a ton of static DNS entries. What I noticed is that still once a day or so, at uneven intervals, CPU will still peg at 100% with DNS consuming it all. I have come to believe that it is tied to flash memory and that the number of static entries I have must be the cause of that. I think there is some housekeeping thread that may be causing this rather poor use of resources.
Fri Jun 06, 2014 4:41 pm
Same problem on my RB751G-2HnD. Profile shows 80% usage on DNS. Disallowing remote requests helps, but it not solution for this problem. I created packet filter rule, that drops DNS requests (UDP traffic on port 53) from all but local subnet (192.168.0.0/24). CPU usage drops from 70-80% to 3-4%, and profiling not showing DNS percentage. It seems that some bots use Mikrotik as DNS-server for some purposes and genering lots of requests.
Fri Oct 31, 2014 1:08 am
Just bumping this old request as the most likely cause is that you are having DNS attacks from outside your network since you have allow remote connections open. You need to firewall that up.
Fri Jan 16, 2015 4:32 pm
Same problem on my RB751G-2HnD. Profile shows 80% usage on DNS. Disallowing remote requests helps, but it not solution for this problem. I created packet filter rule, that drops DNS requests (UDP traffic on port 53) from all but local subnet (192.168.0.0/24). CPU usage drops from 70-80% to 3-4%, and profiling not showing DNS percentage. It seems that some bots use Mikrotik as DNS-server for some purposes and genering lots of requests.
Hey seidizem, it seems you are right.
I saw lots of posts around the internet, where people even change their hardware thinking they got bottle neck on their cpu usage.
I had same problem on my 951G-2HnD and the firewall rule together nat for the DNS requests, solved my problem.
Tue Feb 09, 2016 8:30 pm
Hello, this work for me
/ip firewall filter
add action=drop chain=input dst-port=53 in-interface=wan protocol=udp
Fri Apr 29, 2016 5:43 pm
Fri Apr 29, 2016 6:10 pm
It is not the good method. This article describes only to block port 53 but in fact you should block all
new input packets from the internet interface.
Note that this is already the default. When you have a problem you have either modified the default
firewall, or you have modified the internet port without adjusting the firewall accordingly.
(this happens because of sub-optimal configuration of the default firewall, which they don't want to fix)
When you use PPPoE make sure that the interface "ether1-gateway" in the firewall is changed to your
PPPoE interface in the rule that drops incoming traffic from that interface.
Trainer
Thu Mar 09, 2017 6:53 am
The main issue of DNS is that it does not support multi-thread. It can load only one CPU and it`s easy to reach 100%. In this case even powerful CCR1072 is nothing against DNS request. If DNS service supports multi-thread, would be very nice.
Thu Mar 09, 2017 1:53 pm
A good place to see these attacks visually is under the connections tab on firewall. Knowing the total number of connections under normal use is a good way to spot abnormal traffic. As an example, on my home router, I know that anything over 5 or 600 connections means something weird is happening.
When your DNS ports are open to the internet, you will have multiple thousands of connections on port 53 UDP. Under the connections tab, you will spot this instantly.
Trainer
Fri Mar 24, 2017 9:21 am
In case of DNS attack, it something very easy to stop/block. In case of my hotspot routers, lot of clients ask DNS from the router and CCR1072 become slow on DNS query. But actually CCR1072 can handle thousands of hotspot clients except DNS server role. I implemented separate DNS server to handle it, which I hate when RouterOS supports DNS server.
Fri Mar 24, 2017 3:42 pm
I think the limit in DNS query handling for normal usage is not as much the CPU usage but
a limit in the number of unanswered queries, apparently some table inside the DNS server.
When lots of queries are forwarded, at some point this table becomes full.
Fri Mar 24, 2017 5:14 pm
To anyone having this problem - the first thing to check is whether your router is being used as a DDoS amplifier.
As stated earlier in the thread, look in the firewall connections table for DNS traffic on the WAN interface. If you see DNS traffic to/from anything other than the router's configured DNS resolvers, then you're being exploited in a DDoS because your firewall rules aren't blocking it.
This is a very common issue on the forums here.
Block all incoming new requests on the WAN interface in the INPUT chain of the FILTER firewall rules! If you require some kind of admin access from the WAN side, then make one rule which allows exactly the port you requre (e.g. Winbox) and only from your known remote site(s) which require access. Place this exception earlier in the INPUT chain than the default "throw away everything on the WAN interface" rule, and you're set.
General resource menu shows overall resource usage and router statistics like uptime, memory usage, disk usage, version etc.
It also has several sub-menus for more detailed hardware statistics like PCI, IRQ and USB.
Один комментарий на “ Mikrotik 100% загрузка процессора ”
А почему нельзя совсем закрыть 53-й порт снаружи, у вас на нем сервер для запросов снаружи ?
Properties
All properties are read-only
| Property | Description |
|---|---|
| architecture-name (string) | CPU architecture. Can be powerpc, x86, mipsbe or mipsle. |
| bad-blocks (percent) | Shows percentage of bad blocks on the NAND. |
| board-name (string) | RouterBOARD model name |
| cpu (string) | Cpu model that is on the board. |
| cpu-count (integer) | Number of CPUs present on the system. Each core is separate CPU, Intel HT is also separate CPU. |
| cpu-frequency (string) | Current CPU frequency. |
| cpu-load (percent) | Percentage of used CPU resources. Combines all CPUs. Per-core CPU usage can be see in CPU submenu |
| free-hdd-space (string) | Free space on hard drive or NAND |
| free-memory (string) | Unused amount of RAM |
| platform (string) | Platform name, usually it is "MikroTik" |
| total-hdd-space (string) | Size of the hard drive or NAND |
| total-memory (string) | Amount of installed RAM |
| uptime (time) | Time interval passed since boot-up. |
| version (string) | Installed RouterOS version number. |
| write-sect-since-reboot (integer) | Number of sector writes in HDD or nand since router was last time rebooted. |
| write-sect-total (integer) | Number of sector writes in total. |
Sub-menu level: /system resource cpu
This submenu shows per-cpu usage, as long as IRQ and Disk usage.
IRQ Load Balancing
Sub-menu level: /system resource usb
This menu displays all available USB controllers on the board. Menu is available only if at least one USB controller is present.
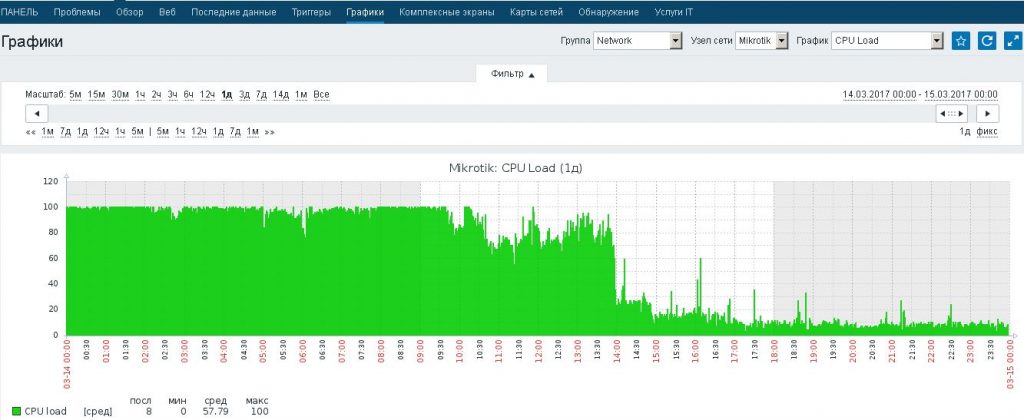
В последние несколько дней пользователи жаловались на нестабильную работу сети. Mikrotik был установлен пару месяцев назад, настроено резервирование канала и работал без сбоев. Тут нужно сказать, что я использую zabbix для мониторинга за некоторыми событиями из журналов windows на своих серверах, а mikrotik был подключен к zabbix ради интереса. Через snmp собирается статистика о загрузке cpu, ram, температуры и т. д. На графике загрузки процессора была видна загрузка CPU на 100% последние несколько дней. Немного погуглив, нашел интересную статью о о борьбе с dns флудом. Интернет раздают два провайдера, подключенных через PPPoE. Один — с динамическим ip, второй — c статическим ip.
Для начала заходим в Tools -> Profile или выполняем в консоли команду ‘tools ptofile‘ и смотрим какой из процессов грузит процессор. В моем случае это оказалась служба dns.
Дальше смотрим, что творится на внешних интерфейса через Tools -> Torch. В Interface выбираем wan интерфейс, ставим чекбоксы на Port и Protocol и нажиманм Start.
В моем случае с внешнего IP второго провайдера уходят пакеты по 53 порту (DNS).
Добавил два правила в IP -> Firewall -> Filter
Через несколько часов загрузка процессора снизилась до приемлемого уровня
Properties
All properties are read-only
| Property | Description |
|---|---|
| architecture-name (string) | CPU architecture. Can be powerpc, x86, mipsbe or mipsle. |
| bad-blocks (percent) | Shows percentage of bad blocks on the NAND. |
| board-name (string) | RouterBOARD model name |
| cpu (string) | Cpu model that is on the board. |
| cpu-count (integer) | Number of CPUs present on the system. Each core is separate CPU, Intel HT is also separate CPU. |
| cpu-frequency (string) | Current CPU frequency. |
| cpu-load (percent) | Percentage of used CPU resources. Combines all CPUs. Per-core CPU usage can be see in CPU submenu |
| free-hdd-space (string) | Free space on hard drive or NAND |
| free-memory (string) | Unused amount of RAM |
| platform (string) | Platform name, usually it is "MikroTik" |
| total-hdd-space (string) | Size of the hard drive or NAND |
| total-memory (string) | Amount of installed RAM |
| uptime (time) | Time interval passed since boot-up. |
| version (string) | Installed RouterOS version number. |
| write-sect-since-reboot (integer) | Number of sector writes in HDD or nand since router was last time rebooted. |
| write-sect-total (integer) | Number of sector writes in total. |
Sub-menu level: /system resource cpu
This submenu shows per-cpu usage, as long as IRQ and Disk usage.
Properties
| Property | Description |
|---|---|
| cpu (integer) | Identification number of CPU which usage is shown. |
| load (percent) | CPU usage in percents |
| irq (percent) | IRQ usage in percents |
| disk (percent) | Disk usage in percents |
Sub-menu level: /system resource irq
Properties
- auto - pick CPU based on number of interrupts. Uses NAPI to optimize interrupts.
Read-only properties
| Property | Description |
|---|---|
| active-cpu (integer) | Shows active CPU in multicore systems. |
| count (integer) | Number of interrupts. On ethernet interfaces interrupt=packet. |
| irq (integer) | IRQ identification number |
| users (string) | Process assigned to IRQ |
Читайте также:


