Lockdown mode vmware что это
To enhance the security measures in a virtualized environment, it is often advisable to limit direct access to Esxi hosts and this is when lockdown mode concept comes into picture. Lockdown mode is used on Esxi hosts in order to improve security of the hosts which are centrally managed by vCenter server.
When the lockdown mode is enabled, the host is managed using the vSphere Client connected to the managing vCenter Server, VMware PowerCLI, or VMware vSphere Command-Line Interface (vCLI). The only difference is that access is authenticated through the vCenter Server instead of using a local account on the ESXi host.
When the lockdown mode is enabled, access to the host through SSH is unavailable except to configured exception users.
Lockdown mode in vSphere 6.0
With vSphere 6.0, VMware introduced a couple of new concepts into lockdown mode as listed below
- Normal Lockdown Mode
- Strict Lockdown Mode
- Exception Users
Lets understand about these concepts one by one.
Normal Lockdown mode

However in this mode the DCUI service is not stopped and If the Esxi host connection to the vCenter Server is lost and access through the vSphere Web Client is no longer available, privileged accounts can log in to the ESXi host’s DCUI and exit lockdown mode.
In normal lockdown mode, only the following accounts can access the DCUI:
- Accounts in the Exception User list for lockdown mode who have administrative privileges on the host. The Exception Users list is meant for service accounts that perform very specific tasks. Exception users do not lose their privileges when the host enters lockdown mode.
- Users defined in the DCUI.Access advanced option for the host: This option is for emergency access to the Direct Console Interface in case the connection to vCenter Server is lost. These users do not require administrative privileges on the host.
Strict Lockdown Mode
In strict lockdown mode, the DCUI service is stopped. If the connection to vCenter Server is lost and the vSphere Web Client is no longer available, the ESXi host becomes unavailable unless the ESXi Shell and SSH services are enabled and Exception Users are defined. If you cannot restore the connection to the vCenter Server system, you have to reinstall the host.
If “Strict Lockdown Mode” is enabled on an ESXi 6.0 host, you will get the following error messages when you try to connect to host via DCUI:
“Authentication Denied – Direct console access has been disabled by the administrator”

Enable/Disable Esxi host Lockdown mode from the vSphere Web Client
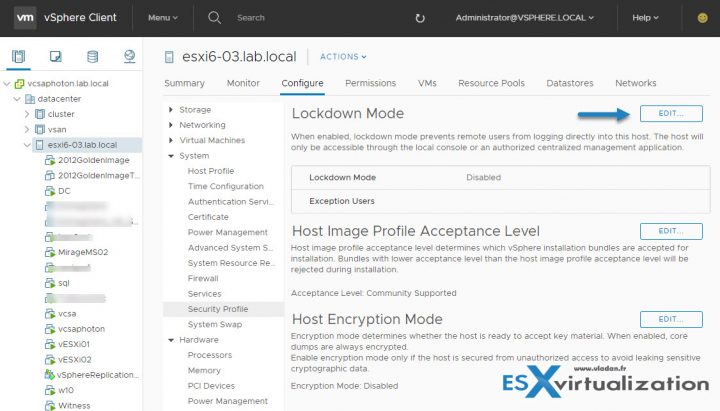
Login to vSphere Web Client and select the Esxi host and navigate to Manage > Settings > Security Profile.
In the Lockdown Mode panel, click Edit.

Click Lockdown Mode and select one of the lockdown mode options.
Lets say we have enabled Normal mode lockdown


But we can login to host via DCUI and can manage host settings from there.

Lets change the mode to strict mode now. Web client will warn you about DCUI sevrices will be stopped in strict mode. Click OK to proceed.

In strict mode, access to DCUI will be denied.

Enable/Disable Lockdown mode from the DCUI:
Login to Esxi host directly via DCUI and under System Customization, select Configure Lockdown Mode setting to enable/disable the lockdown mode.


Note: You can only enable “Normal Lockdown mode” from the DCUI. Which makes sense, because if you do not have a vCenter Server, you will lock yourself out.
What happens to existing user sessions When Lockdown Mode Is Enabled?
If users are logged in to the ESXi Shell or access the host through SSH before lockdown mode is enabled, those users who are on the list of Exception Users and who have administrator privileges on the host remain logged in. The session is terminated for all other users. This applies to both normal and strict lockdown mode.
Configure a User on the Lockdown Mode Exception Users List
Exception users are host local users or Active Directory users with privileges defined locally for the ESXi host. They are not members of an Active Directory group and are not vCenter Server users.
Exception users do not lose their privileges when the host enters lockdown mode. Usually these accounts represent third-party solutions and external applications that need to continue to function in lockdown mode.
To configure exception users, login to vSphere Web Client and select an Esxi host and navigate to Manage > Settings > Security Profile > Lockdown mode.
Click on Edit button and select Exception Users tab and click the green + button to add a user.

Add Users To The DCUI.Access Advanced Option
The main purpose of the DCUI.Access advanced option is to allow you to exit lockdown mode in case of catastrophic failure, when you cannot access the host from vCenter Server . You add users to the list by editing the Advanced Settings for the host from the vSphere Web Client .
However, caution needs to be taken because this can directly impact the security posture of the host(s). Keep in mind, exception users can only perform tasks for which they have privileges for.
1: Browse to the host in the vSphere Web Client object navigator.
2: Click the Manage tab and select Settings .
3: Click Advanced System Settings and search for DCUI.Access .

C lick Edit and enter the user names, separated by commas. By default, the root user is included.

Note: If you are adding a local user here, then that user should be present on Esxi host.

And thats it for this post.
Additional Reading
I hope you find this post informational. Feel free to share this on social media if it is worth sharing. Be sociable 🙂
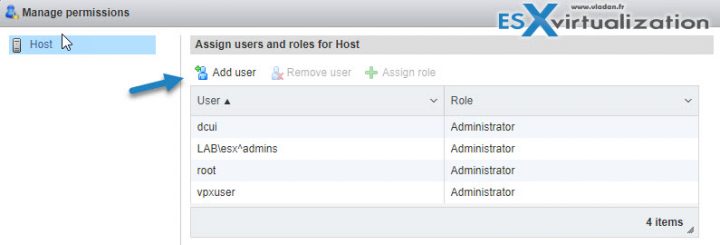
Вот то, что известно всем: vpxuser – учетная запись, используемая vCenter`ом для управления ESXi хостами (опрос гипервизора, отправка задачи), которые в него включены. Т.е. учетная запись root (ESXi) не имеет отношения к связи vCenter – ESXi (за исключением того нюанса, что она нужна для включения ESXi в vCenter).
Vpxuser имеет права администратора ESXi. Таким образом, администратор vCenter`а может выполнять практически все те же самые манипуляции с хостом, что и root (ESXi), кроме создания/удаления/изменения локальных пользователей и групп самого ESXi хоста.
Управлять учетной записью vpxuser с помощью службы каталогов AD нельзя.
Пароль vpxuser хранится в зашифрованном виде и на ESXi и в базе vCenter (логично, не правда ли?) и для каждого ESXi этот пароль уникален.
Подключение к ESXi с помощью VPXUSER
В некоторых источниках я видел утверждения вроде этого: «Знание пароля от vpxuser Вам ничего не даст, использовать эту комбинацию для подключения к хосту и любых других целей невозможно». Однако, зная пароль vpxuser, можно подключиться к ESXi и управлять им (опробовано на Standalone ESXi 5.5 u1 и на ESXi 5.5 u1 под управлением vCenter 5.5, и не только на них).

С другой стороны, узнать пароль vpxuser нельзя (по крайней мере я способ так и не нашел), поэтому подключиться таким образом можно только изменив пароль vpxuser, а этого делать не нужно (читаем дальше).
Изменение пароля VPXUSER
В документации можно обнаружить предупреждение, которое в вольном (моем) переводе выглядит так:
Интересно и другое: далее в этой статье есть информация о политике паролей vpxuser, и по умолчанию длина его пароля 32 символа. Если менять его пароль вручную на ESXi, например с помощью “passwd”, то можно задать пароль намного короче. Видимо, связано это с тем, что политику паролей поддерживает vCenter, а поскольку меняется пароль vpxuser тоже vCenter`ом, то, как говорится «Я своей смешною рожей сам себя и веселю». Т.е. сменить-то пароль можно, и задать его несоответствующим политике можно, но связь с ESXi в итоге будет утеряна.
Потеря связи вполне логична, ведь при ручной смене пароля vpxuser, его пароль в базе vCenter`а не меняется.
Вывод: не меняйте пароль на vpxuser сами, пусть этим занимается vCenter. Если вы изменили пароль vpxuser руками, то с вероятностю 99% рано или поздно vCenter потеряет связь с ESXi. 1% я оставляю на магическое вмешательство.
Устранение проблем
Если все-таки изменения в vpxuser были внесены (например, изменен пароль) и это повлекло недоступность ESXi из vCenter (обычно сопровождается ошибкой: "Call «ServiceInstance.RetrieveContent» for object «ServiceInstance» on Server «ip_address» failed"), то можно поступить следующим образом (если lockdown mode не включен и есть доступ к хосту по SSH):
- ПКМ на хосте в vSphere Client`е, disconnect (если, конечно, хост уже не находится в таком состоянии). НЕ УДАЛЯТЬ хост из vCenter`а.
- Подключиться по SSH к хосту и выполнить: “userdel vpxuser”.
- ПКМ на хосте и выбрать “Connect”. Игнорировать все возможные ошибки аутентификации.
- Ввести требуемый логин root и его пароль. Учетная запись vpxuser будет пересоздана.
Здесь стоит обратить внимание на фразу «если не включен lockdown mode». Если пароль vpxuser был изменен и vCenter потерял связь с ESXi и при этом lockdown mode включен, т.е. доступ к хосту ESXi запрещен всем кроме vCenter, то официальная позиция VMware на этот счет однозначна: «переустанавливайте ESXi».
Политика паролей для vpxuser
Время действия пароля
По умолчанию пароль vpxuser обновляется каждые 30 дней, но это можно изменить:
1. В vSphere Client → Administration.
2. vCenter Server Settings… → Advanced Settings.
3. Выбрать параметр VirtualCenter.VimPasswordExpirationInDays, установить нужное значение.
4. Перезагрузить службу vCenter.

Изменять этот параметр VMware не рекомендует. VMware вообще много чего не рекомендует делать, жить вредно, от этого умирают.
Сложность пароля
Пароль vpxuser состоит из 32х символов, и содержит минимум 1 символ из групп: специальные символы ( и др.), цифры (1-9), большие буквы (латиница) и строчные буквы (латиница).
В документации указано, что для изменения длины пароля vpxuser можно изменить значение параметра vpxd.hostPasswordLength в файле конфигурации на vCenter:
- Linux (VCSA) — /etc/vmware-vpx/vpxd.cfg;
- Windows – C:\ProgramData\VMware\VMware VirtualCenter\vpxd.cfg;
Т.е. внутрь vpxd, но не внутрь какого-либо другого вложенного тега.
Вывод: зачем вообще менять политику паролей для vpxuser? Да незачем, VMware не рекомендует заниматься подобной ерундой.
В разных релизах
Здесь должен быть какой-то вывод
Вывод касательно vpxuser предельно прост — это одна из тех вещей, которые тюнить не стоит практически ни при каких обстоятельствах. Пост призван лишь рассказать чуть больше об этой учетной записи, о ее присутствии в разных релизах и о мифах, вроде того, что её нельзя использовать для прямого подключения к ESXi.
In order to make your ESXi hosts more secure, you can put them what's called Lockdown mode. This post will explain What is VMware ESXi Lockdown Mode, what's the main benefits and the configuration steps. The config is a simple radio button via vSphere web client, but there is also a possibility to activate it through the Direct Console User Interface (DCUI). This is another post for our Tips category.
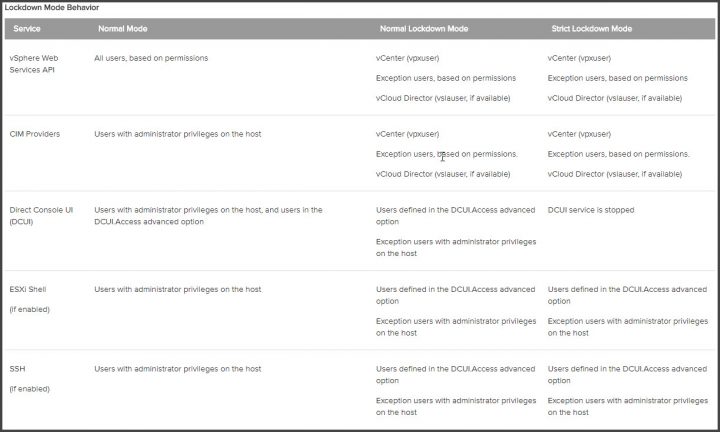
This is the first time we treat this topic and It's important to know what services and restrictions apply in each mode. VMware ESXi Lockdown Mode applies not only to users but also to CIM providers or applications using which needs to keep running (ex. backups).
ESXi lockdown mode has been introduced in ESXi 5.0 in its simpler version, which has been expanded with ESXi 6.0 and ESXi 6.5. If you put the host into a lockdown mode, you can only connect and manage your hosts and your VMs through vCenter Server. Your connection is denied if you want to connect directly to the host via host client.
In lockdown mode, operations must be performed through vCenter Server by default. It was in vSphere 6.0 first where you can choose either between a normal lockdown mode or strict lockdown mode.
ESXi user accounts which are on a special list called Exception Users, which has administrator's privileges and those users can also log in to the ESXi shell through DCUI, or Host client.
Where to Activate VMware ESXi Lockdown Mode?
In order to activate lockdown mode, you can use vSphere Web client or vSphere HTML5 Client.
Select your host > Configure > System > Security Profile > Edit.
VMware ESXi Lockdown Mode – two different modes.
Let's have a look what's the difference between Normal and Strick Lockdown Mode:
Normal Lockdown Mode – The host can be accessed through vCenter Server. Only users who are on the Exception Users list and have administrator privileges can log in to the Direct Console User Interface. If SSH or the ESXi Shell is enabled, access might be possible.
Strict Lockdown Mode – The host can only be accessed through vCenter Server. If SSH or the ESXi Shell is enabled, running sessions for accounts in the DCUI.Access advanced option and for Exception User accounts that have administrator privileges remain enabled. All other sessions are terminated.
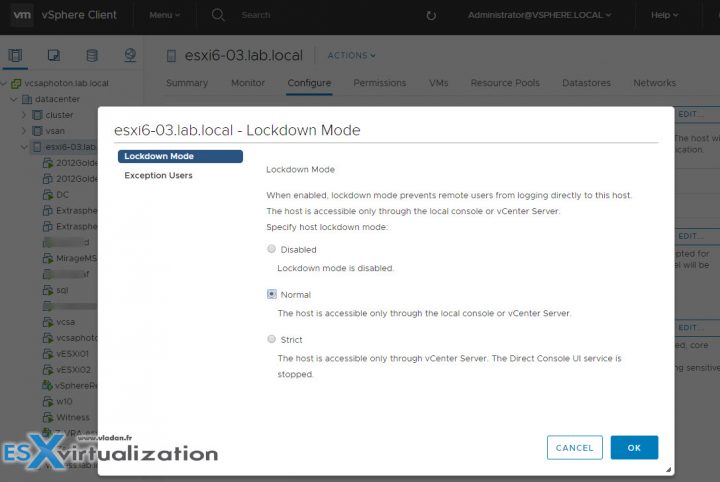
In addition, when selecting the Strict Lockdown mode, the DCUI service is completely stopped.

DC Scope for VMware vSphere – optimization, capacity planning, and cost management. Download FREE Trial Here.
- Tracks the performance of VMs with a summary view of the resources and metrics in degradation.
- Easily improve the performance of your infrastructure.
- DC Scope is affordably priced per VM.
What are the Exception Users?
VMware says that those are users that…
A list of user accounts that keep their permissions when the host enters lockdown mode. The accounts are used by third-party solutions and external applications that must continue their function in lockdown mode. To keep lockdown mode uncompromised, you should add only user accounts that are associated with applications.
Where to add an account to the Exception Users list?
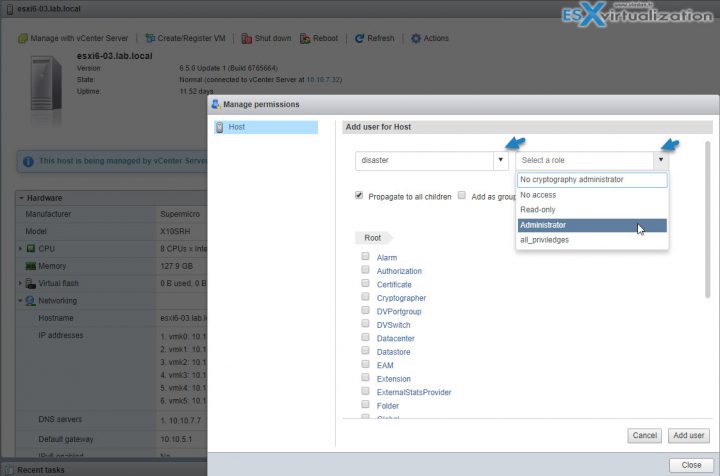
You'd have to first create a local ESXi user and then specify this advanced settings on per-host base. So in my case, I created a sample local ESXi user called “disaster” through ESXi host client which is a local ESXi user.
So in order to modify the Exception users list, you'll have to use the vSphere HTML5 client of vSphere Web Client. To access this setting you Select your host > System > Advanced System Settings > within the list find the DCUI.Access > click to add another local ESXi user there. The root user is already present there by default.
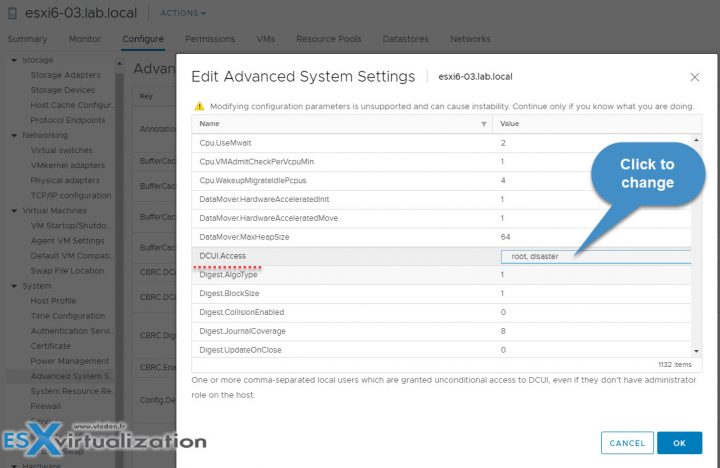
The exception users can only perform tasks for which they have privileges for. So even if you create your local user and put him on the Exceptions list, the user won't be able to connect unless you give him a privilege.
Connect to the ESXi host via ESXi Host Client > Actions > Permissions.
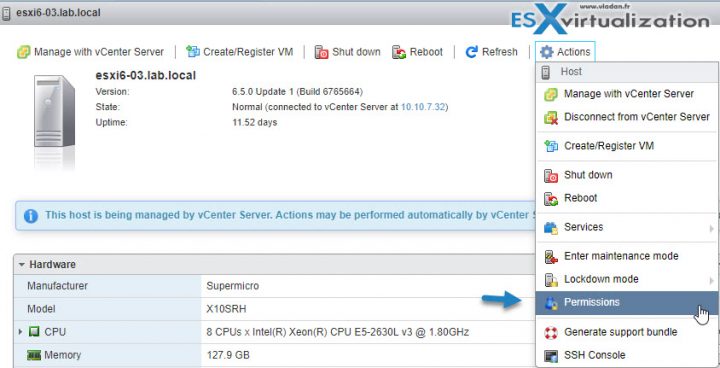
Then Click Add User
The UI will change and here you have the possibility to pick the user you have previously created and then assign a privilege to this user.
VMware has a nice table showing exactly which services or which behaviors are different for Normal and for a Strict Locked mode. This behavior has an influence on the vSphere Web services API, CIM providers, DCUI, ESXi Shell and SSH…..
The table can be found at VMware Documentation Center – Link.
So In which mode I'll be able to log in through the DCUI?
Only if the Standard lockdown mode is activated. Not in the Strict mode.
What if vCenter server is unavailable?
Configure Lockdown Mode will be grayed out if vCenter is down or the host is disconnected from vCenter.
Enable/Disable ESXi lockdown mode from DCUI
Note: This applies if a host is in Normal lockdown mode only. Otherwise you would be able to lock yourself out from within the DCUI.
In the server room:
Open server console > Press F2 to Customize System/View Logs > Open Configure Lockdown Mode > Press SPACE to enable or disable lockdown mode
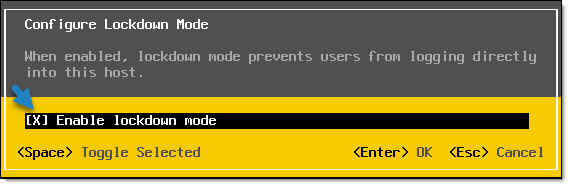
Press ENTER to save the changes. This is it.
Wrap Up:
VMware ESXi Lockdown Mode users from logging directly to the host. The host will only be accessible through a local console or vCenter Server. If there are local ESXi users configured, if they have enough privileges to log in locally AND if they are on the Exceptions list of the lockdown more, then they CAN login locally via Host client.
A very powerful mode indeed, which does not influence on the default root user (unless you remove the root user from the Exceptions list).
You have to think twice before activating the VMware ESXi Lockdown Mode, the “strict” one. If this mode is ON, you removed ALL users from Exceptions AND you lost vCenter server connection between this particular host and your vCenter, then have a big problem. You won't be able to log in locally.
To increase the security of your ESXi hosts, you can put them in lockdown mode. In lockdown mode, all operations must be performed through vCenter Server. Only the vpxuser user has authentication
permissions, no other users can perform operations against the host directly.
Lockdown mode basically means that your host is configured to allow connections only from vCenter, with the only user with permissions to log onto the host being the vpxuser account. As lockdown mode only allows connections from vCenter, vCLI and vMA will not be able to interact with the host directly and will need to be used with vCenter instead.
Lockdown mode can be enabled when adding the host to vCenter using the vSphere client, in the hosts security options in the vSphere client, or by using the dcui (Direct Console User Interface).
Using the vSphere Client to Configure Lockdown Mode
The Lockdown Mode configuration can be found under the Configuration | Security Profile settings:

Once enabled, you will only be able to access the host by connecting to vCenter or directly, using the DCUI. To enable or disable using the DCUI, log in and then select ‘Configure Lockdown Mode’:

Configuring Lockdown Mode using the CLI
You can check if lockdown mode is enabled using the CLI by running:
To enable lockdown mode:
And to disable lockdown mode:
Configuring Total Lockdown Mode
Total lockdown mode, in addition to the restrictions put in place by lockdown mode, further restricts access by disabling the DCUI. This means that there is no way to access the host, or disable lockdown mode, other than through vCenter. If access to vCenter is lost then the host would need to have ESXi reinstalled.
To enable total lockdown mode you first need to enable lockdown mode as shown above. Next you need to disable access to the DCUI by stopping the DCUI service and setting it to manual startup:

Written by Sam McGeown on 26/9/2013 · Read in about 4 min (715 words)
This article is now 9 years old! It is highly likely that this information is out of date and the author will have completely forgotten about it. Please take care when following any guidance to ensure you have up-to-date recommendations.

This is the first article in a series of vSphere Security articles that I have planned. The majority of this article is based on vSphere/ESXi 5.1, though I will include any 5.5 information that I find relevant.
I think lockdown mode is a feature that is rarely understood, and even more rarely used. Researching this article I’ve already encountered several different definitions that weren’t quite right. As far as I can see there are no differences between lockdown more in 5.5 and 5.1.
The vSphere Security guide says (emphasis mine):
To increase the security of your ESXi hosts, you can put them in lockdown mode. _In lockdown mode, all
operations must be performed through vCenter Server_. Only the vpxuser user has authentication
permissions, no other users can perform operations against the host directly.
In short, lockdown mode means you can ONLY manage the host via vCenter. The only exception is via the DCUI.
Enabling lockdown mode
Enabling lockdown mode is really simple, it’s a tick box on the vSphere Client, WebClient or the DCUI.
Select a host, select “Configuration” (vSphere Client) or “Manage” then “Settings” (Web Client) and then “Security Profile”


To do it via the DCUI, log in to the host and select “Configure Lockdown Mode”

One thing to note here is enabling lockdown mode via the DCUI behaves differently to the vSphere or Web clients! As per the documentation:
If you enable or disable lockdown mode using the Direct Console User Interface (DCUI), _permissions
for users and groups on the host are discarded._ To preserve these permissions, you must enable and disable
lockdown mode using the vSphere Web Client connected to vCenter Server.
When you disable lockdown mode using the DCUI, all users with the DCUI Access privilege
are granted the Administrator role on the host
Testing access with lockdown mode
I tested each of these options on one of my domain joined hosts using the following tests:
- SSH – I enabled SSH and the Firewall exception on the host and tested using PuTTY to log in.
- PowerCLI* – I connected to the host directly using Connect-VIServer
- vSphere Client – I connected using the vSphere Client, for domain users I tested with Windows session credentials and manually entered credentials.
- DCUI – I tested logging on at the console of the server.
*Note that PowerCLI connected through vCenter can still manage hosts, you can even use Get-EsxCli.
The below chart is the results of my testing, which matches the table in VMware’s document pretty well:


With lockdown mode enabled, Direct Console User Interface (DCUI) access is allowed for root, and any user specified with the DCUI.Access advanced option. My testing showed this can include domain users.

Total Lockdown Mode
VMware’s document also describes a “Total Lockdown Mode”, which basically means using a combination of Lockdown mode enabled and disabling the services for SSH, DCUI and ESXi Shell. There is no “enable total lockdown mode” button. In this configuration if you lose your vCenter Server you have one option only: rebuild ESXi. This would be an extremely secure configuration, but it would negate the possibility of troubleshooting if you lost contact with your vCenter Server.
Why use lockdown mode?
I think this is the most difficult aspect of lockdown mode. In my opinion you need a clear set of security requirements to implement it (as with all security). You need to consider usability – would you rather SSH into a host to troubleshoot than stand in the unpleasant environment of a data center? You can argue that OOB management such as iLO, DRAC or IMM allows you to remotely access the console, but then how secure is your remote management password? Are you closing off one attack vector in favour of another?
The use case that makes most sense to me for lockdown mode is for hosts in the DMZ. Even then I favour a properly isolated management network that mitigates the risk and allows you to keep the management of your hosts separate from Virtual Machine traffic. If you follow VMware’s design best practices a “Fully Collapsed DMZ” does just that.
I’d love to hear from any reader who uses lockdown mode in a production environment, and the use case for it, I personally have never heard from anyone who does!
Читайте также:


