Как удалить checkpoint endpoint security с компьютера
Are you in need of uninstalling Check Point VPN to fix some problems? Are you looking for an effective solution to completely uninstall it and thoroughly delete all of its files out of your PC? No worry! This page provides detailed instructions on how to completely uninstall Check Point VPN.
Possible problems when you uninstall Check Point VPN
* Check Point VPN is not listed in Programs and Features.
* You do not have sufficient access to uninstall Check Point VPN.
* A file required for this uninstallation to complete could not be run.
* An error has occurred. Not all of the files were successfully uninstalled.
* Another process that is using the file stops Check Point VPN being uninstalled.
* Files and folders of Check Point VPN can be found in the hard disk after the uninstallation.
Check Point VPN cannot be uninstalled due to many other problems. An incomplete uninstallation of Check Point VPN may also cause many problems. So, it's really important to completely uninstall Check Point VPN and remove all of its files.
How to Uninstall Check Point VPN Completley?
Recommended Method: Quick Way to Uninstall Check Point VPN
Method 1: Uninstall Check Point VPN via Programs and Features.
Method 2: Uninstall Check Point VPN with its uninstaller.exe.
Method 3: Uninstall Check Point VPN via System Restore.
Method 4: Uninstall Check Point VPN with Antivirus.
Method 5: Reinstall Check Point VPN to uninstall.
Method 6: Use the Uninstall Command Displayed in the Registry.
Method 7: Uninstall Check Point VPN with Third-party Uninstaller.
Method 1: Uninstall Check Point VPN via Programs and Features.
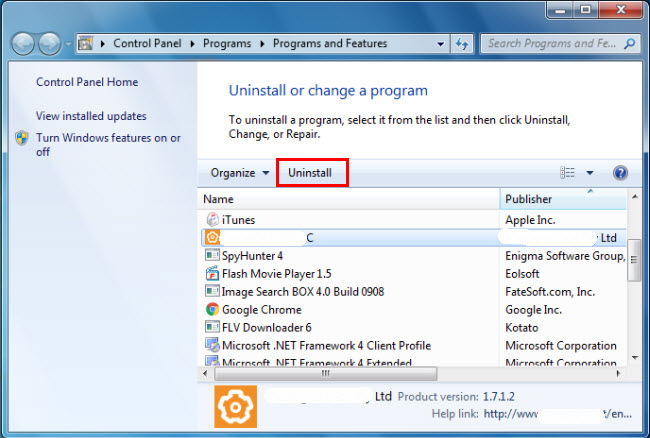
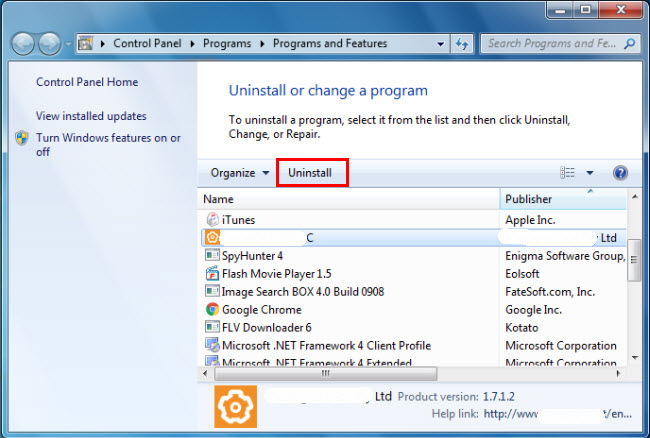
When a new piece of program is installed on your system, that program is added to the list in Programs and Features. When you want to uninstall the program, you can go to the Programs and Features to uninstall it. So when you want to uninstall Check Point VPN, the first solution is to uninstall it via Programs and Features.
Steps:
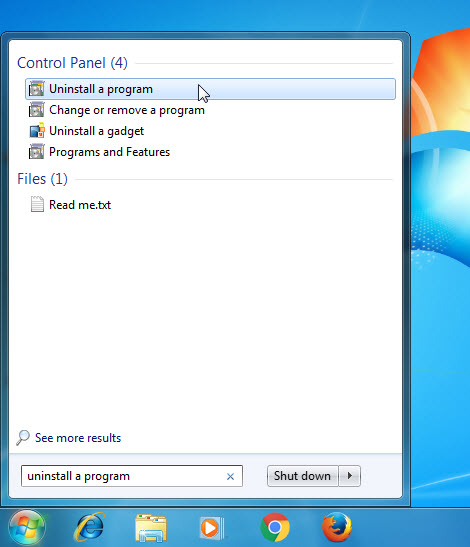
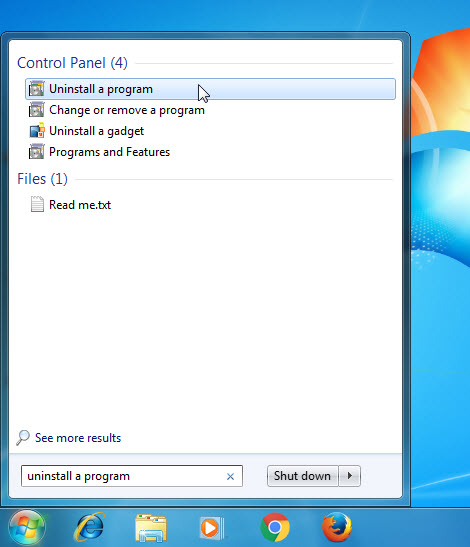
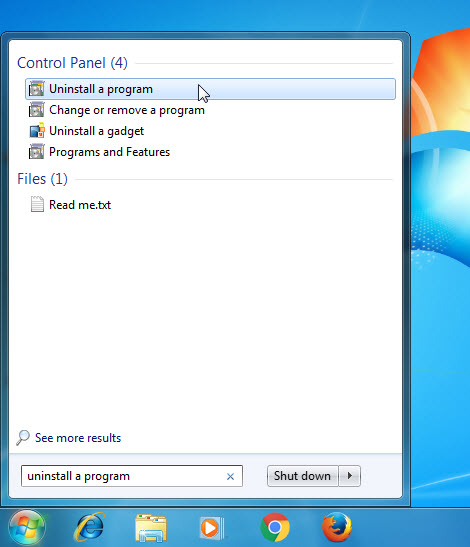
a. Open Programs and Features.
Windows Vista and Windows 7
Click Start, type uninstall a program in the Search programs and files box and then click the result.
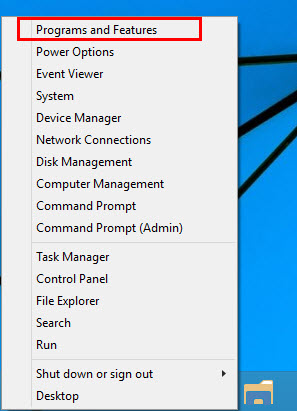
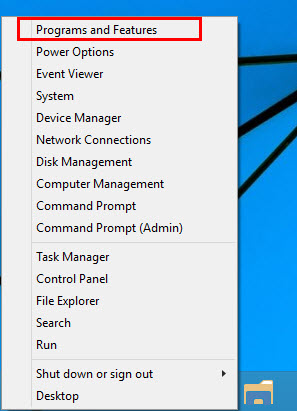
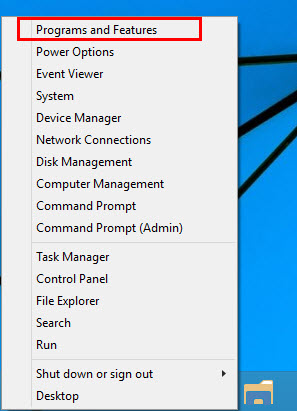
Windows 8, Windows 8.1 and Windows 10
Open WinX menu by holding Windows and X keys together, and then click Programs and Features.
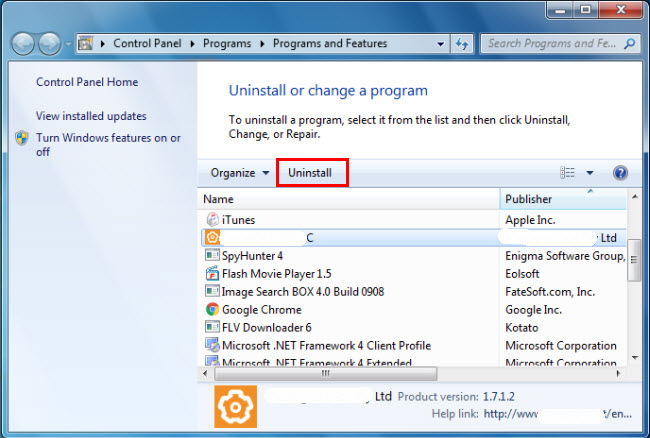
b. Look for Check Point VPN in the list, click on it and then click Uninstall to initiate the uninstallation.
Method 2: Uninstall Check Point VPN with its uninstaller.exe.
Most of computer programs have an executable file named uninst000.exe or uninstall.exe or something along these lines. You can find this files in the installation folder of Check Point VPN.
Steps:
a. Go to the installation folder of Check Point VPN.
b. Find uninstall.exe or unins000.exe.
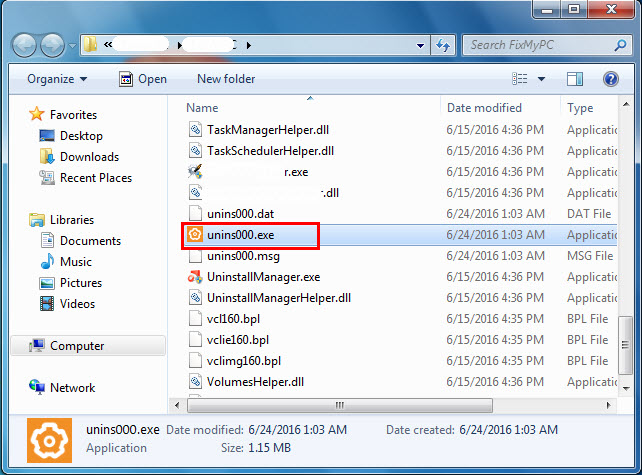
c. Double click on its uninstaller and follow the wizard to uninstall Check Point VPN.
Method 3: Uninstall Check Point VPN via System Restore.
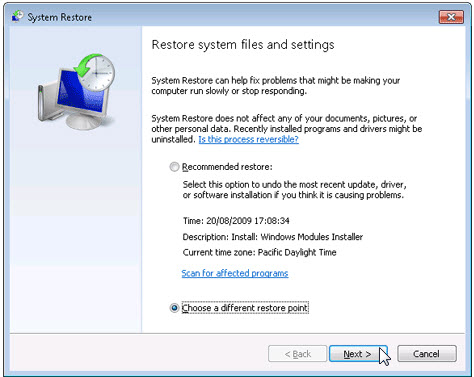
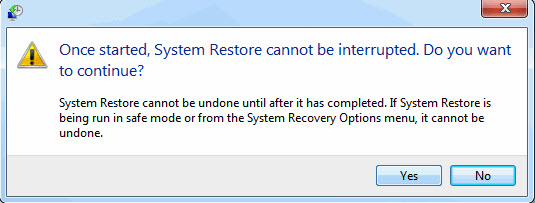
System Restore is a utility which comes with Windows operating systems and helps computer users restore the system to a previous state and remove programs interfering with the operation of the computer. If you have created a system restore point prior to installing a program, then you can use System Restore to restore your system and completely eradicate the unwanted programs like Check Point VPN. You should backup your personal files and data before doing a System Restore.
Steps:
a. Close all files and programs that are open.
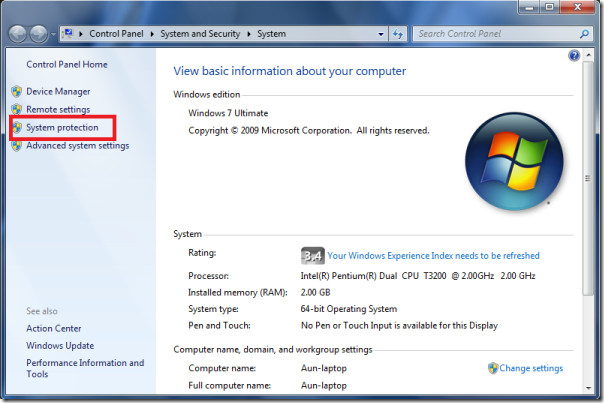
b. On the desktop, right click Computer and select Properties. The system window will display.
c. On the left side of the System window, click System protection. The System Properties window will display.
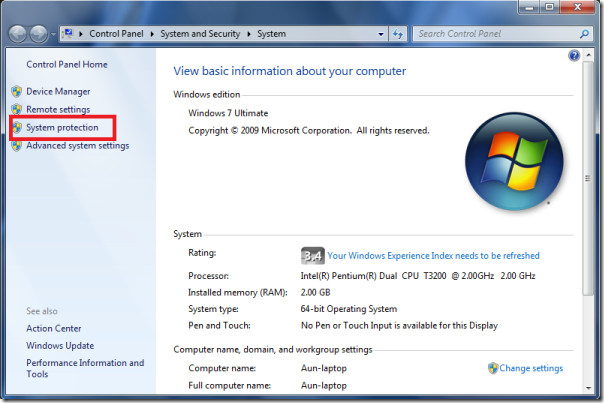
d. Click System Restore and the System Restore window will display.

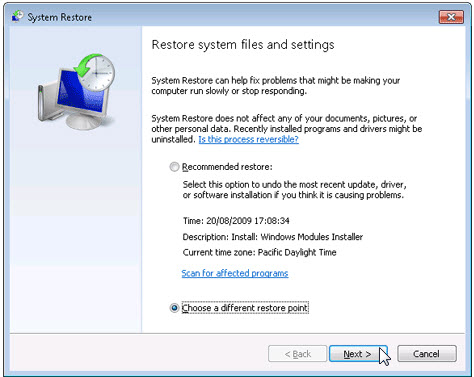
e. Select Choose a different restore point and click Next.
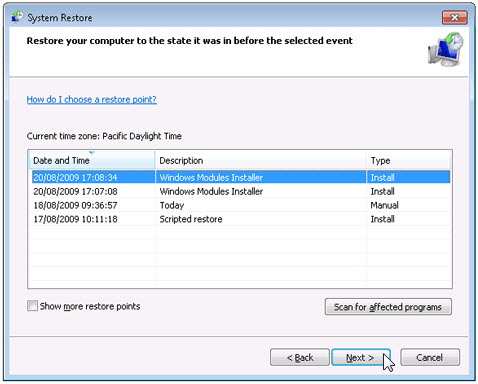
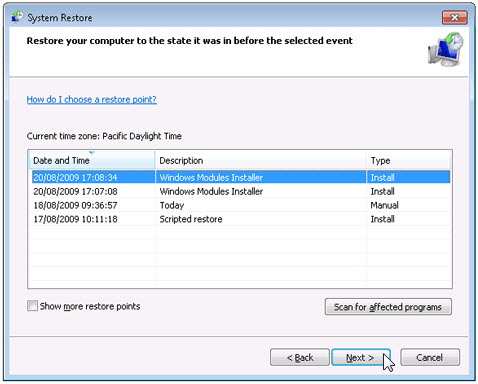
f. Select a date and time from the list and then click Next. You should know that all programs and drivers installed after the selected date and time may not work properly and may need to be re-installed.
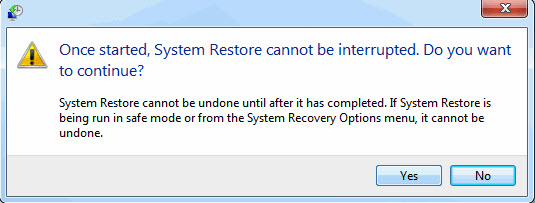
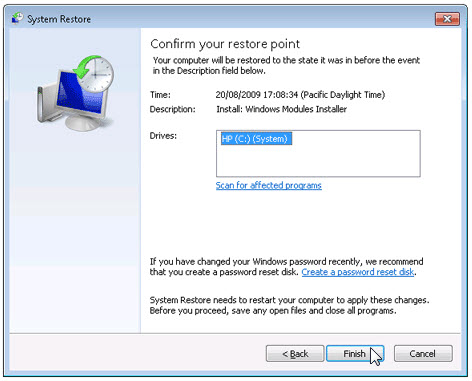
g. Click Finish when the "Confirm your restore point" window appears.
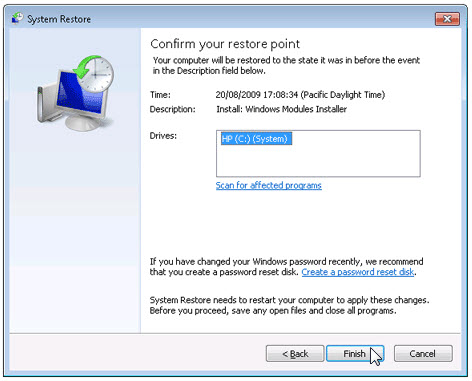
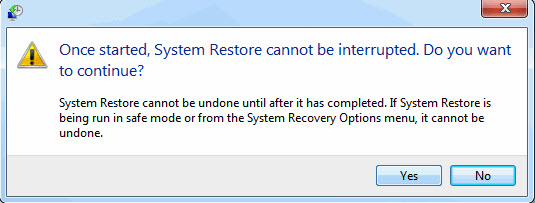
h. Click Yes to confirm again.
Method 4: Uninstall Check Point VPN with Antivirus.
Nowadays, computer malware appear like common computer applications but they are much more difficult to remove from the computer. Such malware get into the computer with the help of Trojans and spyware. Other computer malware like adware programs or potentially unwanted programs are also very difficult to remove. They usually get installed on your system by bundling with freeware software like video recording, games or PDF convertors. They can easily bypass the detection of the antivirus programs on your system. If you cannot remove Check Point VPN like other programs, then it's worth checking whether it's a malware or not. Click and download this malware detect tool for a free scan.
Method 5: Reinstall Check Point VPN to Uninstall.
When the file required to uninstall Check Point VPN is corrupted or missing, it will not be able to uninstall the program. In such circumstance, reinstalling Check Point VPN may do the trick. Run the installer either in the original disk or the download file to reinstall the program again. Sometimes, the installer may allow you to repair or uninstall the program as well.
Method 6: Use the Uninstall Command Displayed in the Registry.
When a program is installed on the computer, Windows will save its settings and information in the registry, including the uninstall command to uninstall the program. You can try this method to uninstall Check Point VPN. Please carefully edit the registry, because any mistake there may make your system crash.
Steps:
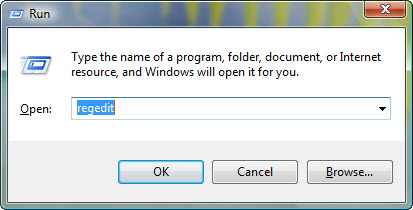
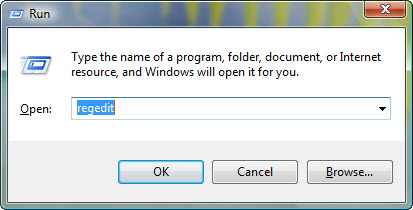
a. Hold Windows and R keys to open the Run command, type in regedit in the box and click OK.
b. Navigate the following registry key and find the one of Check Point VPN:
c. Double click on the UninstallString value, and copy its Value Data.
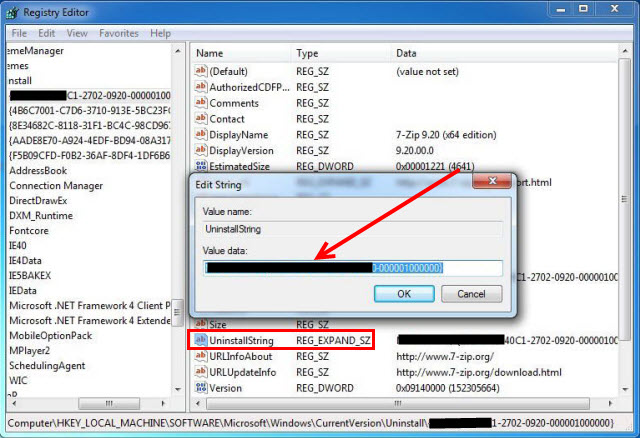
d. Hold Windows and R keys to open the Run command, paste the Value Data in the box and click OK.
e. Follow the wizard to uninstall Check Point VPN.
Method 7: Uninstall Check Point VPN with Third-party Uninstaller.
The manual uninstallation of Check Point VPN requires computer know-how and patience to accomplish. And no one can promise the manual uninstallation will completely uninstall Check Point VPN and remove all of its files. And an incomplete uninstallation will many useless and invalid items in the registry and affect your computer performance in a bad way. Too many useless files also occupy the free space of your hard disk and slow down your PC speed. So, it's recommended that you uninstall Check Point VPN with a trusted third-party uninstaller which can scan your system, identify all files of Check Point VPN and completely remove them. Download this powerful third-party uninstaller below.
Are you in need of uninstalling Check Point Endpoint Security to fix some problems? Are you looking for an effective solution to completely uninstall it and thoroughly delete all of its files out of your PC? No worry! This page provides detailed instructions on how to completely uninstall Check Point Endpoint Security.
Possible problems when you uninstall Check Point Endpoint Security
* Check Point Endpoint Security is not listed in Programs and Features.
* You do not have sufficient access to uninstall Check Point Endpoint Security.
* A file required for this uninstallation to complete could not be run.
* An error has occurred. Not all of the files were successfully uninstalled.
* Another process that is using the file stops Check Point Endpoint Security being uninstalled.
* Files and folders of Check Point Endpoint Security can be found in the hard disk after the uninstallation.
Check Point Endpoint Security cannot be uninstalled due to many other problems. An incomplete uninstallation of Check Point Endpoint Security may also cause many problems. So, it's really important to completely uninstall Check Point Endpoint Security and remove all of its files.
How to Uninstall Check Point Endpoint Security Completley?
Recommended Method: Quick Way to Uninstall Check Point Endpoint Security
Method 1: Uninstall Check Point Endpoint Security via Programs and Features.
Method 2: Uninstall Check Point Endpoint Security with its uninstaller.exe.
Method 3: Uninstall Check Point Endpoint Security via System Restore.
Method 4: Uninstall Check Point Endpoint Security with Antivirus.
Method 5: Reinstall Check Point Endpoint Security to uninstall.
Method 6: Use the Uninstall Command Displayed in the Registry.
Method 7: Uninstall Check Point Endpoint Security with Third-party Uninstaller.
Method 1: Uninstall Check Point Endpoint Security via Programs and Features.
When a new piece of program is installed on your system, that program is added to the list in Programs and Features. When you want to uninstall the program, you can go to the Programs and Features to uninstall it. So when you want to uninstall Check Point Endpoint Security, the first solution is to uninstall it via Programs and Features.
Steps:
a. Open Programs and Features.
Windows Vista and Windows 7
Click Start, type uninstall a program in the Search programs and files box and then click the result.
Windows 8, Windows 8.1 and Windows 10
Open WinX menu by holding Windows and X keys together, and then click Programs and Features.
b. Look for Check Point Endpoint Security in the list, click on it and then click Uninstall to initiate the uninstallation.
Method 2: Uninstall Check Point Endpoint Security with its uninstaller.exe.
Most of computer programs have an executable file named uninst000.exe or uninstall.exe or something along these lines. You can find this files in the installation folder of Check Point Endpoint Security.
Steps:
a. Go to the installation folder of Check Point Endpoint Security.
b. Find uninstall.exe or unins000.exe.
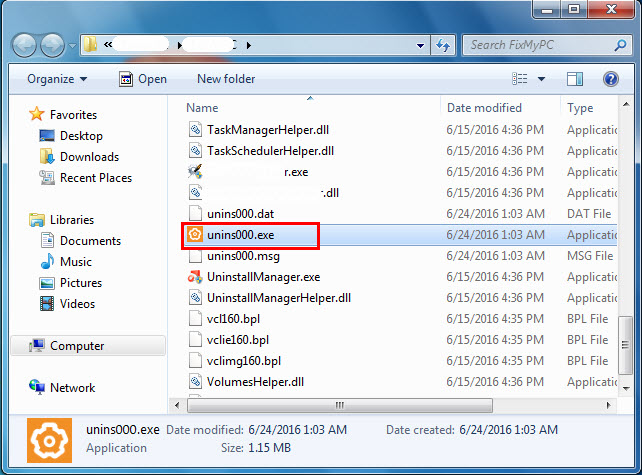
c. Double click on its uninstaller and follow the wizard to uninstall Check Point Endpoint Security.
Method 3: Uninstall Check Point Endpoint Security via System Restore.
System Restore is a utility which comes with Windows operating systems and helps computer users restore the system to a previous state and remove programs interfering with the operation of the computer. If you have created a system restore point prior to installing a program, then you can use System Restore to restore your system and completely eradicate the unwanted programs like Check Point Endpoint Security. You should backup your personal files and data before doing a System Restore.
Steps:
a. Close all files and programs that are open.
b. On the desktop, right click Computer and select Properties. The system window will display.
c. On the left side of the System window, click System protection. The System Properties window will display.
d. Click System Restore and the System Restore window will display.

e. Select Choose a different restore point and click Next.
f. Select a date and time from the list and then click Next. You should know that all programs and drivers installed after the selected date and time may not work properly and may need to be re-installed.
g. Click Finish when the "Confirm your restore point" window appears.
h. Click Yes to confirm again.
Method 4: Uninstall Check Point Endpoint Security with Antivirus.
Nowadays, computer malware appear like common computer applications but they are much more difficult to remove from the computer. Such malware get into the computer with the help of Trojans and spyware. Other computer malware like adware programs or potentially unwanted programs are also very difficult to remove. They usually get installed on your system by bundling with freeware software like video recording, games or PDF convertors. They can easily bypass the detection of the antivirus programs on your system. If you cannot remove Check Point Endpoint Security like other programs, then it's worth checking whether it's a malware or not. Click and download this malware detect tool for a free scan.
Method 5: Reinstall Check Point Endpoint Security to Uninstall.
When the file required to uninstall Check Point Endpoint Security is corrupted or missing, it will not be able to uninstall the program. In such circumstance, reinstalling Check Point Endpoint Security may do the trick. Run the installer either in the original disk or the download file to reinstall the program again. Sometimes, the installer may allow you to repair or uninstall the program as well.
Method 6: Use the Uninstall Command Displayed in the Registry.
When a program is installed on the computer, Windows will save its settings and information in the registry, including the uninstall command to uninstall the program. You can try this method to uninstall Check Point Endpoint Security. Please carefully edit the registry, because any mistake there may make your system crash.
Steps:
a. Hold Windows and R keys to open the Run command, type in regedit in the box and click OK.
b. Navigate the following registry key and find the one of Check Point Endpoint Security:
c. Double click on the UninstallString value, and copy its Value Data.
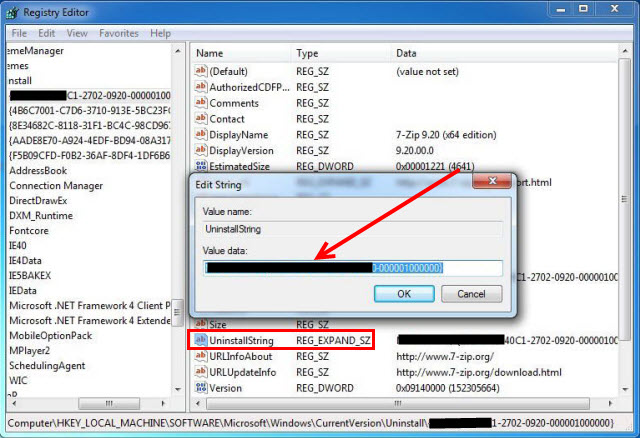
d. Hold Windows and R keys to open the Run command, paste the Value Data in the box and click OK.
e. Follow the wizard to uninstall Check Point Endpoint Security.
Method 7: Uninstall Check Point Endpoint Security with Third-party Uninstaller.
The manual uninstallation of Check Point Endpoint Security requires computer know-how and patience to accomplish. And no one can promise the manual uninstallation will completely uninstall Check Point Endpoint Security and remove all of its files. And an incomplete uninstallation will many useless and invalid items in the registry and affect your computer performance in a bad way. Too many useless files also occupy the free space of your hard disk and slow down your PC speed. So, it's recommended that you uninstall Check Point Endpoint Security with a trusted third-party uninstaller which can scan your system, identify all files of Check Point Endpoint Security and completely remove them. Download this powerful third-party uninstaller below.
Join the CHECKMATES Everywhere Competition
Submit your picture to win!
Check Point Proactive support
Free trial available for 90 Days!
As YOU DESERVE THE BEST SECURITY
Upgrade to our latest GA Jumbo
The 2022 MITRE Engenuity ATT&CK®
Evaluations Results Are In!
Now Available: SmartAwareness Security Training
Training Built to Educate and Engage
MITRE ATT&CK
Inside Check Point products!
CheckFlix!
All Videos In One Space
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- CheckMates
- :
- Products
- :
- Harmony
- :
- Endpoint
- :
- Uninstall Check Point Endpoint Security without Un.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Email to a Friend
I found a conversation very similar to my situation.
In this case - there was no registry entry for HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\CheckPoint\Endpoint Security and adding two entries allowed the default password to be used to uninstall this software.
I'm trying to remove the software - without knowing the uninstall password - but when I check my registry I have a bunch of entries under:
There are UninstPwdHash & UninstPwdSalt entries along with others.
I added the suggested UninstPwdSaltDA & UninstPwdHashDA with values of 0 but I am still receiving the error of invalid password.
I'm hoping someone can help me in that I see that I can either:
- Remove these existing values & hope the new DA values will be in effect
- Update these existing values to 0
- Remove the newly added DA entries - change the existing to add DA suffix to their name and set their value to 0
I'm afraid if I mess something up too bad then I may not be able to get back into my machine.
Any/all help is welcome.

G_W_Albrecht
- Mark as New
- Bookmark
- Subscribe
- Mute
- Email to a Friend
I see the following solution possibilities, but they all require access to an EPS Server, the first two to the EPS that also deployed your agent .
- if your EPS client is connected to the Server and an E84.30 client or above, configure uninstall by Push Operation > Add > Agent Settings > Uninstall Client . This is pushed to the client and you will see the status in EPS.
- if your EPS client is connected to the Server, simply change the uninstall password in Common Client policy in the Policies tab ( sk61168), client will update the registry values and uninstall is possible
- if not, deploy a new client with known uninstall password to another machine and copy the 2 UninstPwdHash & UninstPwdSalt entries from it to your registry. Now you should be able to uninstall using sk118233. This does not need the original EPS Server at all, so you could also do a eval lab deployment.
PhoneBoy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Email to a Friend
I recommend engaging with the TAC on this.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Email to a Friend
You already followed this sk right?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Email to a Friend
Yes - the solution assumes I have the uninstall password - which I do not. In fact, this is where I started before I added the two entries with DA suffixes. Thanks.

G_W_Albrecht
- Mark as New
- Bookmark
- Subscribe
- Mute
- Email to a Friend
I see the following solution possibilities, but they all require access to an EPS Server, the first two to the EPS that also deployed your agent .
- if your EPS client is connected to the Server and an E84.30 client or above, configure uninstall by Push Operation > Add > Agent Settings > Uninstall Client . This is pushed to the client and you will see the status in EPS.
- if your EPS client is connected to the Server, simply change the uninstall password in Common Client policy in the Policies tab ( sk61168), client will update the registry values and uninstall is possible
- if not, deploy a new client with known uninstall password to another machine and copy the 2 UninstPwdHash & UninstPwdSalt entries from it to your registry. Now you should be able to uninstall using sk118233. This does not need the original EPS Server at all, so you could also do a eval lab deployment.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Email to a Friend
I'm in a similar situation as TechnoJock: my uninstall password does not work.
I already created a new uninstall password and pushed this out to the clients. I consider that this was successesful as I can see that the new policy is shown on the client. But even with this new password it does not work.
@G_W_Albrecht: you mentioned in your last post that there is a possibility to push out a client uninstall task. But I don't have this option available in my console. Can you maybe specify with version of the management server/console is necessary to have this option?
We are in the process of re-deploying > 100 windows clients. Due to the COVID situation these clients are spread across Europe and the removing the CheckPoint client is one of the major obstacles in this process.
Unfortunately Management decided not to continue with CheckPoint so I don't have the possibility to open a TAC case.
Are you in need of uninstalling Check Point Endpoint Security - Secure Access to fix some problems? Are you looking for an effective solution to completely uninstall it and thoroughly delete all of its files out of your PC? No worry! This page provides detailed instructions on how to completely uninstall Check Point Endpoint Security - Secure Access.
Possible problems when you uninstall Check Point Endpoint Security - Secure Access
* Check Point Endpoint Security - Secure Access is not listed in Programs and Features.
* You do not have sufficient access to uninstall Check Point Endpoint Security - Secure Access.
* A file required for this uninstallation to complete could not be run.
* An error has occurred. Not all of the files were successfully uninstalled.
* Another process that is using the file stops Check Point Endpoint Security - Secure Access being uninstalled.
* Files and folders of Check Point Endpoint Security - Secure Access can be found in the hard disk after the uninstallation.
Check Point Endpoint Security - Secure Access cannot be uninstalled due to many other problems. An incomplete uninstallation of Check Point Endpoint Security - Secure Access may also cause many problems. So, it's really important to completely uninstall Check Point Endpoint Security - Secure Access and remove all of its files.
How to Uninstall Check Point Endpoint Security - Secure Access Completley?
Recommended Method: Quick Way to Uninstall Check Point Endpoint Security - Secure Access
Method 1: Uninstall Check Point Endpoint Security - Secure Access via Programs and Features.
Method 2: Uninstall Check Point Endpoint Security - Secure Access with its uninstaller.exe.
Method 3: Uninstall Check Point Endpoint Security - Secure Access via System Restore.
Method 4: Uninstall Check Point Endpoint Security - Secure Access with Antivirus.
Method 5: Reinstall Check Point Endpoint Security - Secure Access to uninstall.
Method 6: Use the Uninstall Command Displayed in the Registry.
Method 7: Uninstall Check Point Endpoint Security - Secure Access with Third-party Uninstaller.
Method 1: Uninstall Check Point Endpoint Security - Secure Access via Programs and Features.
When a new piece of program is installed on your system, that program is added to the list in Programs and Features. When you want to uninstall the program, you can go to the Programs and Features to uninstall it. So when you want to uninstall Check Point Endpoint Security - Secure Access, the first solution is to uninstall it via Programs and Features.
Steps:
a. Open Programs and Features.
Windows Vista and Windows 7
Click Start, type uninstall a program in the Search programs and files box and then click the result.
Windows 8, Windows 8.1 and Windows 10
Open WinX menu by holding Windows and X keys together, and then click Programs and Features.
b. Look for Check Point Endpoint Security - Secure Access in the list, click on it and then click Uninstall to initiate the uninstallation.
Method 2: Uninstall Check Point Endpoint Security - Secure Access with its uninstaller.exe.
Most of computer programs have an executable file named uninst000.exe or uninstall.exe or something along these lines. You can find this files in the installation folder of Check Point Endpoint Security - Secure Access.
Steps:
a. Go to the installation folder of Check Point Endpoint Security - Secure Access.
b. Find uninstall.exe or unins000.exe.
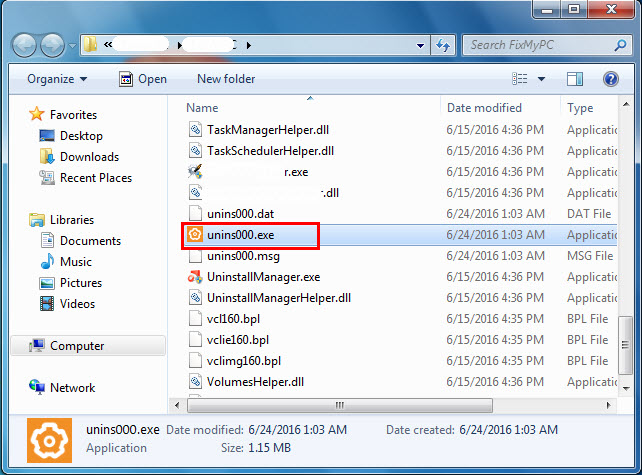
c. Double click on its uninstaller and follow the wizard to uninstall Check Point Endpoint Security - Secure Access.
Method 3: Uninstall Check Point Endpoint Security - Secure Access via System Restore.
System Restore is a utility which comes with Windows operating systems and helps computer users restore the system to a previous state and remove programs interfering with the operation of the computer. If you have created a system restore point prior to installing a program, then you can use System Restore to restore your system and completely eradicate the unwanted programs like Check Point Endpoint Security - Secure Access. You should backup your personal files and data before doing a System Restore.
Steps:
a. Close all files and programs that are open.
b. On the desktop, right click Computer and select Properties. The system window will display.
c. On the left side of the System window, click System protection. The System Properties window will display.
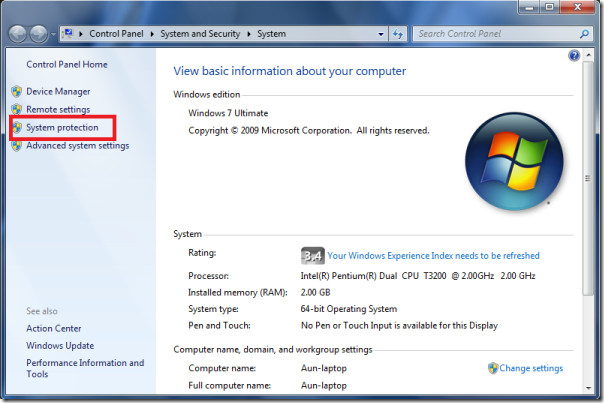
d. Click System Restore and the System Restore window will display.

e. Select Choose a different restore point and click Next.
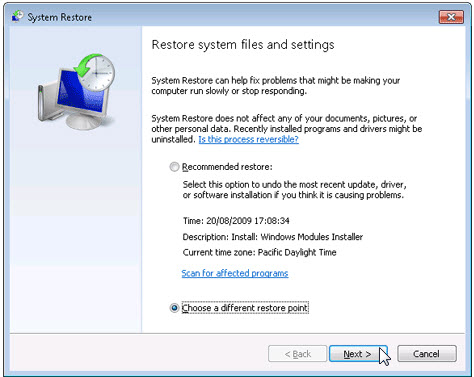
f. Select a date and time from the list and then click Next. You should know that all programs and drivers installed after the selected date and time may not work properly and may need to be re-installed.
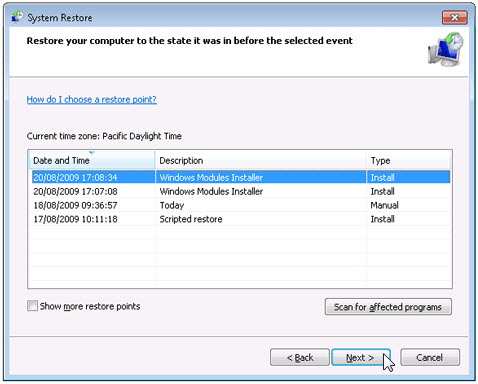
g. Click Finish when the "Confirm your restore point" window appears.
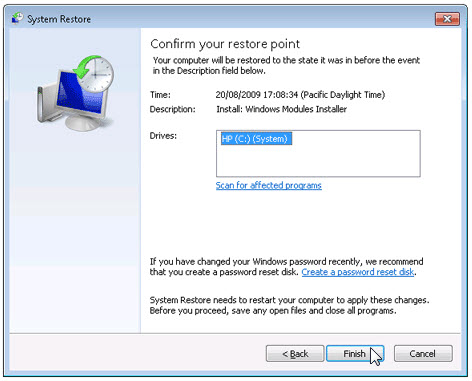
h. Click Yes to confirm again.
Method 4: Uninstall Check Point Endpoint Security - Secure Access with Antivirus.
Nowadays, computer malware appear like common computer applications but they are much more difficult to remove from the computer. Such malware get into the computer with the help of Trojans and spyware. Other computer malware like adware programs or potentially unwanted programs are also very difficult to remove. They usually get installed on your system by bundling with freeware software like video recording, games or PDF convertors. They can easily bypass the detection of the antivirus programs on your system. If you cannot remove Check Point Endpoint Security - Secure Access like other programs, then it's worth checking whether it's a malware or not. Click and download this malware detect tool for a free scan.
Method 5: Reinstall Check Point Endpoint Security - Secure Access to Uninstall.
When the file required to uninstall Check Point Endpoint Security - Secure Access is corrupted or missing, it will not be able to uninstall the program. In such circumstance, reinstalling Check Point Endpoint Security - Secure Access may do the trick. Run the installer either in the original disk or the download file to reinstall the program again. Sometimes, the installer may allow you to repair or uninstall the program as well.
Method 6: Use the Uninstall Command Displayed in the Registry.
When a program is installed on the computer, Windows will save its settings and information in the registry, including the uninstall command to uninstall the program. You can try this method to uninstall Check Point Endpoint Security - Secure Access. Please carefully edit the registry, because any mistake there may make your system crash.
Steps:
a. Hold Windows and R keys to open the Run command, type in regedit in the box and click OK.
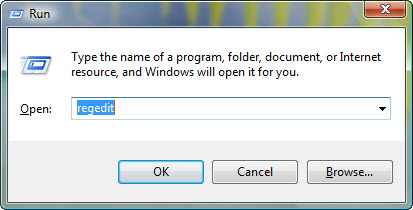
b. Navigate the following registry key and find the one of Check Point Endpoint Security - Secure Access:
c. Double click on the UninstallString value, and copy its Value Data.
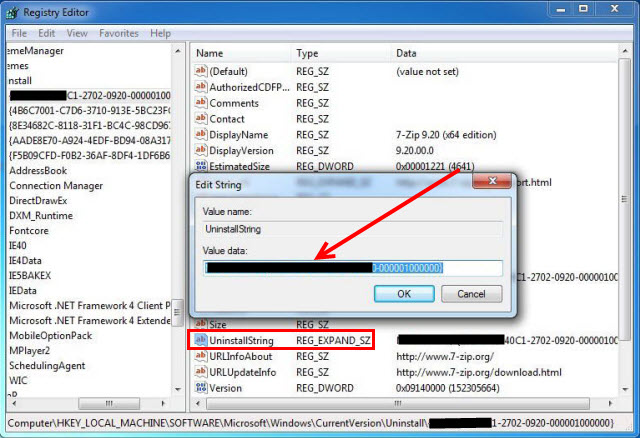
d. Hold Windows and R keys to open the Run command, paste the Value Data in the box and click OK.
e. Follow the wizard to uninstall Check Point Endpoint Security - Secure Access.
Method 7: Uninstall Check Point Endpoint Security - Secure Access with Third-party Uninstaller.
The manual uninstallation of Check Point Endpoint Security - Secure Access requires computer know-how and patience to accomplish. And no one can promise the manual uninstallation will completely uninstall Check Point Endpoint Security - Secure Access and remove all of its files. And an incomplete uninstallation will many useless and invalid items in the registry and affect your computer performance in a bad way. Too many useless files also occupy the free space of your hard disk and slow down your PC speed. So, it's recommended that you uninstall Check Point Endpoint Security - Secure Access with a trusted third-party uninstaller which can scan your system, identify all files of Check Point Endpoint Security - Secure Access and completely remove them. Download this powerful third-party uninstaller below.
TrGUI.exe это исполняемый файл, который является частью Check Point Endpoint Security Программа, разработанная Check Point, Inc, Программное обеспечение обычно о 331.64 MB по размеру.
Расширение .exe имени файла отображает исполняемый файл. В некоторых случаях исполняемые файлы могут повредить ваш компьютер. Пожалуйста, прочитайте следующее, чтобы решить для себя, является ли TrGUI.exe Файл на вашем компьютере - это вирус или троянский конь, который вы должны удалить, или это действительный файл операционной системы Windows или надежное приложение.

TrGUI.exe безопасный, или это вирус или вредоносная программа?
Первое, что поможет вам определить, является ли тот или иной файл законным процессом Windows или вирусом, это местоположение самого исполняемого файла. Например, такой процесс, как TrGUI.exe, должен запускаться из C: \ Program Files \ checkpoint \ endpoint connect \ tracsrvwrapper.exe и нигде в другом месте.
Для подтверждения откройте диспетчер задач, выберите «Просмотр» -> «Выбрать столбцы» и выберите «Имя пути к изображению», чтобы добавить столбец местоположения в диспетчер задач. Если вы обнаружите здесь подозрительный каталог, возможно, стоит дополнительно изучить этот процесс.
Еще один инструмент, который иногда может помочь вам обнаружить плохие процессы, - это Microsoft Process Explorer. Запустите программу (не требует установки) и активируйте «Проверить легенды» в разделе «Параметры». Теперь перейдите в View -> Select Columns и добавьте «Verified Signer» в качестве одного из столбцов.
Если статус процесса «Проверенная подписывающая сторона» указан как «Невозможно проверить», вам следует взглянуть на процесс. Не все хорошие процессы Windows имеют метку проверенной подписи, но ни один из плохих.
Наиболее важные факты о TrGUI.exe:
Если у вас возникли какие-либо трудности с этим исполняемым файлом, перед удалением TrGUI.exe вам следует определить, заслуживает ли он доверия. Для этого найдите этот процесс в диспетчере задач.
Найдите его местоположение (оно должно быть в C: \ Program Files \ CheckPoint \ Endpoint Connect \) и сравните размер и т. Д. С приведенными выше фактами.
Кроме того, функциональность вируса может сама влиять на удаление TrGUI.exe. В этом случае вы должны включить Безопасный режим с загрузкой сетевых драйверов - безопасная среда, которая отключает большинство процессов и загружает только самые необходимые службы и драйверы. Когда вы можете запустить программу безопасности и полный анализ системы.
Могу ли я удалить или удалить TrGUI.exe?
Не следует удалять безопасный исполняемый файл без уважительной причины, так как это может повлиять на производительность любых связанных программ, использующих этот файл. Не забывайте регулярно обновлять программное обеспечение и программы, чтобы избежать будущих проблем, вызванных поврежденными файлами. Что касается проблем с функциональностью программного обеспечения, проверяйте обновления драйверов и программного обеспечения чаще, чтобы избежать или вообще не возникало таких проблем.
Согласно различным источникам онлайн, 6% людей удаляют этот файл, поэтому он может быть безвредным, но рекомендуется проверить надежность этого исполняемого файла самостоятельно, чтобы определить, является ли он безопасным или вирусом. Лучшая диагностика для этих подозрительных файлов - полный системный анализ с Reimage, Если файл классифицирован как вредоносный, эти приложения также удалят TrGUI.exe и избавятся от связанных вредоносных программ.
Однако, если это не вирус, и вам нужно удалить TrGUI.exe, вы можете удалить Check Point Endpoint Security с вашего компьютера, используя программу удаления, которая должна находиться по адресу: MsiExec.exe / X . Если вы не можете найти его деинсталлятор, то вам может понадобиться удалить Check Point Endpoint Security, чтобы полностью удалить TrGUI.exe. Вы можете использовать функцию «Установка и удаление программ» на панели управления Windows.
- 1. в Меню Пуск (для Windows 8 щелкните правой кнопкой мыши в нижнем левом углу экрана), нажмите Панель управления, а затем под Программы:
o Windows Vista / 7 / 8.1 / 10: нажмите Удаление программы.
o Windows XP: нажмите Установка и удаление программ.
- 2. Когда вы найдете программу Check Point Endpoint Securityщелкните по нему, а затем:
o Windows Vista / 7 / 8.1 / 10: нажмите Удалить.
o Windows XP: нажмите Удалить or Изменить / Удалить вкладка (справа от программы).
- 3. Следуйте инструкциям по удалению Check Point Endpoint Security.
Наиболее распространенные ошибки TrGUI.exe, которые могут возникнуть:
• "Ошибка приложения TrGUI.exe."
• «Ошибка TrGUI.exe».
• «Возникла ошибка в приложении TrGUI.exe. Приложение будет закрыто. Приносим извинения за неудобства».
• «TrGUI.exe не является допустимым приложением Win32».
• «TrGUI.exe не запущен».
• «TrGUI.exe не найден».
• «Не удается найти TrGUI.exe».
• «Ошибка запуска программы: TrGUI.exe.»
• «Неверный путь к приложению: TrGUI.exe.»
Аккуратный и опрятный компьютер - это один из лучших способов избежать проблем с Check Point Endpoint Security. Это означает выполнение сканирования на наличие вредоносных программ, очистку жесткого диска cleanmgr и ПФС / SCANNOWудаление ненужных программ, мониторинг любых автозапускаемых программ (с помощью msconfig) и включение автоматических обновлений Windows. Не забывайте всегда делать регулярные резервные копии или хотя бы определять точки восстановления.
Если у вас возникла более серьезная проблема, постарайтесь запомнить последнее, что вы сделали, или последнее, что вы установили перед проблемой. Использовать resmon Команда для определения процессов, вызывающих вашу проблему. Даже в случае серьезных проблем вместо переустановки Windows вы должны попытаться восстановить вашу установку или, в случае Windows 8, выполнив команду DISM.exe / Online / Очистка-изображение / Восстановить здоровье, Это позволяет восстановить операционную систему без потери данных.
Чтобы помочь вам проанализировать процесс TrGUI.exe на вашем компьютере, вам могут пригодиться следующие программы: Менеджер задач безопасности отображает все запущенные задачи Windows, включая встроенные скрытые процессы, такие как мониторинг клавиатуры и браузера или записи автозапуска. Единый рейтинг риска безопасности указывает на вероятность того, что это шпионское ПО, вредоносное ПО или потенциальный троянский конь. Это антивирус обнаруживает и удаляет со своего жесткого диска шпионское и рекламное ПО, трояны, кейлоггеры, вредоносное ПО и трекеры.
Обновлено май 2022 г .:
Мы рекомендуем вам попробовать это новое программное обеспечение, которое исправляет компьютерные ошибки, защищает их от вредоносных программ и оптимизирует производительность вашего ПК. Этот новый инструмент исправляет широкий спектр компьютерных ошибок, защищает от таких вещей, как потеря файлов, вредоносное ПО и сбои оборудования.

(опциональное предложение для Reimage - Cайт | Лицензионное соглашение | Политика конфиденциальности | Удалить)
Загрузите или переустановите TrGUI.exe
Информация об операционной системе
Ошибки TrGUI.exe могут появляться в любых из нижеперечисленных операционных систем Microsoft Windows:
Читайте также:


